Which of the following threats will the use of a privacy screen on a computer help prevent?
A user wants to back up a Windows 10 device. Which of the following should the user select?
A payroll workstation has data on it that needs to be readily available and can be recovered quickly if something is accidentally removed. Which of the following backup methods should be used to provide fast data recovery in this situation?
Which of the following wireless security features can be enabled lo allow a user to use login credentials to attach lo available corporate SSIDs?
A change advisory board authorized a setting change so a technician is permitted to Implement the change. The technician successfully implemented the change. Which of the following should be done next?
Which of the following filesystem types does macOS use?
A user connected a smartphone to a coffee shop's public Wi-Fi and noticed the smartphone started sending unusual SMS messages and registering strange network activity A technician thinks a virus or other malware has infected the device. Which of the following should the technician suggest the user do to best address these security and privacy concerns? (Select two).
A user is receiving repeated pop-up advertising messages while browsing the internet. A malware scan Is unable to locate the source of an infection. Which of the following should the technician check NEXT?
A workstation is displaying a message indicating that a user must exchange cryptocurrency for a decryption key. Which of the following is the best way for a technician to return the device to service safely?
A remote user is experiencing issues connecting to a corporate email account on a laptop. The user clicks the internet connection icon and does not recognize the connected Wi-Fi. The help desk technician, who is troubleshooting the issue, assumes this is a rogue access point. Which of the following is the first action the technician should take?
A systems administrator is experiencing Issues connecting from a laptop to the corporate network using PKI. Which to the following tools can the systems administrator use to help remediate the issue?
A technician removed a virus from a user's device. The user returned the device a week later with the same virus on it. Which of the following should the technician do to prevent future infections?
A company is looking lot a solution that provides a backup for all data on the system while providing the lowest impact to the network. Which of the following backup types will the company MOST likely select?
A user attempts to install additional software and receives a UAC prompt. Which of the following is the BEST way to resolve this issue?
A user's corporate laptop with proprietary work Information was stolen from a coffee shop. The user togged in to the laptop with a simple password. and no other security mechanisms were in place. Which of the following would MOST likely prevent the stored data from being recovered?
Which of the following common security vulnerabilities can be mitigated by using input validation?
Users access files in the department share. When a user creates a new subfolder, only that user can access the folder and Its files. Which of the following will MOST likely allow all users to access the new folders?
The courts determined that a cybercrimes case could no longer be prosecuted due to the agency's handling of evidence. Which of the following was MOST likely violated during the investigation?
Which of The following refers to the steps to be taken if an Issue occurs during a change Implementation?
Every time a user tries to open the organization's proprietary application on an Android tablet, the application immediately closes. Other applications are operating normally. Which of the following troubleshooting actions would MOST likely resolve the Issue? (Select TWO).
A user reported that a laptop's screen turns off very quickly after silting for a few moments and is also very dim when not plugged in to an outlet Everything else seems to be functioning normally. Which of the following Windows settings should be configured?
A technician is unable to access the internet or named network resources. The technician receives a valid IP address from the DHCP server and can ping the default gateway. Which of the following should the technician check next to resolve the issue?
An administrator responded to an incident where an employee copied financial data to a portable hard drive and then left the company with the data. The administrator documented the movement of the evidence. Which of the following concepts did the administrator demonstrate?
Which of the following allows access to the command line in macOS?
A technician sees a file that is requesting payment to a cryptocurrency address. Which of the following should the technician do first?
A help desk technician determines a motherboard has failed. Which of the following is the most logical next step in the remediation process?
Which of the following best describes when to use the YUM command in Linux?
A customer calls the help desk asking for instructions on how to modify desktop wallpaper. Which of the following Windows 10 settings should the technician recommend?
While trying to repair a Windows 10 OS, a technician receives a prompt asking for a key. The technician tries the administrator password, but it is rejected. Which of the following does the technician need in order to continue the OS repair?
A system drive is nearly full, and a technician needs lo tree up some space. Which of the following tools should the technician use?
A user connected an external hard drive but is unable to see it as a destination to save files. Which of the following tools will allow the drive to be formatted?
Which of the following operating systems is considered closed source?
A malicious file was executed automatically when a flash drive was plugged in. Which of the following features would prevent this type of incident?
Which of the following would most likely be used in a small office environment?
A technician discovers user input has been captured by a malicious actor. Which of the following malware types is MOST likely being used?
A user called the help desk lo report an Issue with the internet connection speed on a laptop. The technician thinks that background services may be using extra bandwidth. Which of the following tools should the technician use to investigate connections on the laptop?
A user is experiencing the following issues with Bluetooth on a smartphone:
•The user cannot hear any sound from a speaker paired with the smartphone.
•The user is having issues synchronizing data from their smart watch, which is also connected via Bluetooth.
A technician checked the Bluetooth settings, confirmed it is successfully paired with a speaker, and adjusted the volume levels, but still could not hear anything. Which of the following steps should the technician take next to troubleshoot the Bluetooth issues?
A technician needs to recommend a way to keep company devices for field and home-based staff up to date. The users live in various places across the country and the company has several national offices that staff can go to for technical support Which of the following methods is most appropriate for the users?
A user takes a work-issued laptop home for the first time. When the user attempts to browse any website on the home internet, the user receives the following error:
"This site cannot be reached."
A technician from work confirms that the static IP that was set up on the machine was changed back to DHCP. Which of the following needs to be corrected?
An administrator needs to back up the following components of a single workstation:
•The installation of the operating system
•Applications
•User profiles
•System settings
Which of the following backup methods can the administrator use to ensure the workstation is properly backed up?
A technician is troubleshooting a Windows 10 PC that has experienced a BSOD. The user recently installed optional Windows updates. Which of the following is best way to resolve the issue?
A customer, whose smartphone's screen was recently repaired, reports that the device has no internet access through Wi-Fi. The device shows that it is connected to Wi-Fi, has an address of 192.168.1.42. and has no subnet mask. Which of the following should the technician check next?
A user accidentally installed the incorrect word processing application on an iMac. Which of the following would allow the user to uninstall the incorrect application?
A user opened an infected email. A security administrator responded to the malicious event, successfully mitigated the situation, and returned the machine to service Which of the following needs to be completed before this event is considered closed?
A technician is setting up a network printer for a customer who has a SOHO router. The technician wants to make sure the printer stays connected in the future and is available on all the computers in the house. Which of the following should the technician configure on the printer?
A user’s Windows 10 workstation with an HDD is running really slowly. The user has opened, closed, and saved many large files over the past week. Which of the following tools should a technician use to remediate the issue?
A company uses shared drives as part of a workforce collaboration process. To ensure the correct access permissions, inheritance at the top-level folder is assigned to each department. A manager's team is working on confidential material and wants to ensure only the immediate team can view a specific folder and its subsequent files and subfolders. Which of the following actions should the technician most likely take?
An administrator needs to select a method to dispose of SSDs containing sensitive data. Which of the following are the most appropriate methods? (Select two).
A technician is installing software on a user's workstation. The installation fails due to incompliance with the HCL. Which of the following components is most likely causing the installation to fail? (Select two).
Which of the following languages is used for scripting the creation of Active Directory accounts?
A technician is setting up a new PC in a SOHO. Which of the following should the technician most likely configure on the PC?
A company installed WAPs and deployed new laptops and docking stations to all employees. The docking stations are connected via LAN cables. Users are now reporting degraded network service. The IT department has determined that the WAP mesh network is experiencing a higher than anticipated amount of traffic. Which of the following would be the most efficient way to ensure the wireless network can support the expected number of wireless users?
A technician needs to troubleshoot a user's computer while the user is connected to the system. The technician must also connect to the user's system using remote access tools built in to Windows Which of the following is the best option to troubleshoot the user's computer?
A user wants to back up a device's OS and data. Which of the following is the best way to accomplish this task?
A technician wants to securely dispose of storage drives. Which of the following is the best way to eliminate data on SSDs?
Which of the following features can be used to ensure a user can access multiple versions of files?
A technician is upgrading the Microsoft Windows 10 OS. Which of the following are required for the technician to safely upgrade the OS? (Select two).
A user receives an error message on a Windows 10 device when trying to access a mapped drive from a Windows XP machine in the office. Other Windows XP devices in the office can access the drive. Which of the following Control Panel utilities should the user select to enable connectivity to the device?
A network administrator is setting up the security for a SOHO wireless network. Which of the following options should the administrator enable to secure the network?
Which of the following Linux commands would help to identify which directory the user is currently operating in?
Which of the following features can a technician use to ensure users are following password length requirements?
A technician needs to implement a system to handle both authentication and authorization. Which of the following meets this requirement?
A technician wants to harden Windows workstations after a recent security audit indicated the company is vulnerable to brute-force attacks. Which of the following features should the technician implement to mitigate such attacks?
A user submits a request to have a graphics application installed on a desktop When the technician attempts to install the application, the installation fails and the error message "Not compatible with OS' is displayed. Which of the following is the most likely reason for this error message?
An employee has been using the same password for multiple applications and websites for the past several years. Which of the following would be best to prevent security issues?
A user's computer is running slower than usual and takes a long time to start up. Which of the following tools should the technician use first to investigate the issue?
A customer service representative is unable to send jobs to a printer at a remote branch office. However, the representative can print successfully to a local network printer. Which of the following commands should a technician use to view the path of the network traffic from the PC?
A user received an alert from a Windows computer indicating low storage space. Which of the following will best resolve this issue?
A technician needs to upgrade a legacy system running on a 32-bit OS with new applications that can work both on a 32-bit and a 64-bit system. The legacy system is critically important to the organization. The IT manager cautions that the new applications must not have a detrimental effect on company finances. Which of the following impacts is the IT manager most concerned with?
A network administrator wants to enforce a company's security policy that prohibits USB drives on user workstations. Which of the following commands should the administrator run on the users' workstations?
A customer wants to make sure the data is protected and secure on a Windows laptop's hard drive. Which of the following is the best solution?
A user reports receiving constant, unwanted pop-ups and being unable to close the browser window. These issues have impacted the user's productivity and may have caused the user's files to be altered. Which of the following should a technician do to address these issues with minimal impact to the user?
A technician is installing a new copy of Windows on all computers in the enterprise Given the following requirements:
• The install phase must be scripted to run over the network • Each computer requires a new SSD as the system drive, • The existing HDD should remain as a backup drive.
Which of the following command-line tools should the technician use to install the drive and transfer the installation files from the network share? (Select three).
A technician thinks a customer's computer may have a malware infection and wants to determine whether the computer is in communication with any other machines. Which of the following commands should the technician use?
A customer recently upgraded their computer to the latest Windows version and is now having issues with the display. The icons and text are too large, and the colors are not accurate. Which of the following Control Panel options should the technician adjust to help the customer?
A user reports that a system is performing unusually and is sending requests to an unfamiliar IP address every five minutes. Which of the following should the technician check first to troubleshoot the issue?
A user reports that a device with a statically defined IP is unable to connect to the internet. The technician runs the ipconfig /all command and sees the following output:
IPv4 Address............ 192.168.0.74
Subnet Mask.............255.255.255.255
Default Gateway......... 192.168.0.1
Which of the following is most likely the reason for the issue?
Which of the following types of malicious software is most likely to demand payments in cryptocurrency?
Which of the following operating systems uses the ext4 filesystem type?
A security administrator teaches all of an organization's staff members to use BitLocker To Go. Which of the following best describes the reason for this training?
Which of the following is a situation in which a surge suppressor is considered critical?
Which of the following methods is a way to superficially delete files on a hard drive?
Internet speeds on a user's Windows 10 device are slow, but other devices on the same network are running at normal speeds. A technician thinks the issue may be related to the proxy settings. Which of the following should the technician check to verify the proxy configuration?
A workstation does not recognize a printer. However, the previous day. the printer successfully received a job from the workstation. Which of the following tools should a technician use to see what happened before the failure?
A user's access to a website Is being blocked. Other users on the same network are also unable to access the website. However, when using personal mobile phones not connected to the network, users can access the website. Which of the following is preventing access to the website?
Which of the following is the most secure screen lock?
A company is transitioning to a new firewall and discovers that one of the servers is still sending traffic to the old firewall. Which of the following IP address settings should a technician change to resolve this issue?
A user needs to test several software replacement possibilities. Part of the process involves installing the different software options on a corporate-imaged sandboxed PC. Which of the following is the best option to allow the user to install the required software?
A technician needs to override DNS and map IP addresses and URLs to different locations. Which of the following should the technician do?
A technician is dispatched to a user's office to connect a PC to an office printer. The technician notices several documents on the user's desk that display other technicians' PII. Which of the following should the technician do to maintain proper professionalism?
A user sent a large amount of money to a supplier's bank account and claims that the Chief Executive Officer instructed the user to do so. A technician informs the user that the request was fraudulent and contacts the authorities. Which of the following types of attack took place?
Which of the following is the first step to prevent unauthorized access on a lost mobile device?
Which of the following ensures proprietary information on a lost or stolen mobile device cannot be accessed while the device is offline?
After access to a server room was breached, a technician needs to implement a secure method to prevent unauthorized access. Which of the following is the most secure solution?
A technician received a notification about encrypted production data files and thinks active ransomware is on the network. The technician isolated and removed the suspicious system from the network. Which of the following steps should the technician take next?
A customer is explaining issues with a workstation to a technician. While the customer is listing the issues, the technician is browsing social media on a smartphone. Which of the following professionalism and communication techniques should the technician be using in this situation? (Select two).
A technician, who is completing hardware upgrades at a company, is approached by a user who submitted a computer upgrade request. After checking the list of offices to upgrade, the technician finds that the user's office is not listed for an upgrade. Which of the following actions should the technician take next?
A change management review board denied an administrator's request for change. The administrator had provided the purpose and scope of the change, the date and time, and impacted systems with the risk analysis. Which of the following should be included to approve this change?
A customer needs to purchase a desktop capable of rendering video. Which of the following should the customer prioritize?
Which of the following is protected by government policy for end-user information?
After a computer upgrade at an imaging lab. the upgraded computers are not able to obtain an IP address. Which of the following is most likely the issue?
A technician receives a help desk ticket regarding a software issue on a workstation. The workstation provides the only access to a corporate database, and the technician needs to recover the workstation quickly. Which of the following actions should the technician take?
The user often hosts meetings from a Windows desktop, and meeting participants ask the user to make the text larger when the user shares the computer screen. When not in meetings, the user wants the text be smaller for work tasks. Which of the following is the most efficient way to change text font size?
A user’s personal computer was infected with malware that had a known remediation. Which of the following should the user have done to prevent this issue?
Which of the following features allows a user to install software from a DVD even when the laptop running macOS does not have an optical drive?
A Windows 10 computer is not installing updates and continues to receive errors even during manual update installations. Which of the following should a technician do to fix the issues? (Select two).
Which of the following script file types is typically used to install Windows packages?
Employees want their Windows 10 laptops to wirelessly connect when they take them home. Which of the following should the employees configure so the laptops can automatically connect wirelessly?
During a routine check, a systems administrator discovers that a user's PC is running slowly and CPU utilization is at 100%. Further investigation shows a large amount of resource usage. Which of the following is the most likely cause of the high resource usage?
A user's Android phone has been randomly restarting. A technician investigates and finds several applications have been installed that are not available within the standard marketplace. Which of the following is most likely the cause of the issue?
A technician has verified a computer is infected with malware. The technician isolates the system and updates the anti-malware software. Which of the following should the technician do next?
A technician is trying to connect to a user's laptop in order to securely install updates. Given the following information about the laptop:
Which of the following should the technician do to connect via RDP?
An administrator has submitted a change request for an upcoming server deployment. Which of the following must be completed before the change can be approved?
A Windows computer is experiencing slow performance when the user tries to open programs and files. The user recently installed a new software program from an external website.
Various websites are being redirected to an unauthorized site, and Task Manager shows the CPU usage is consistently at 100%. Which of the following should the technician do first?
Which of the following is used to ensure users have the appropriate level of access to perform their job functions?
A user's iPhone was permanently locked after several failed log-in attempts. Which of the following authentication methods are needed to restore access, applications, and data to the device?
Which of the following environmental factors are most important to consider when planning the configuration of a data center? (Select two).
A user clicks a link in an email. A warning message in the user's browser states the site's certificate cannot be verified. Which of the following is the most appropriate action for a technician to take?
A technician is building a new desktop machine for a user who will be using the workstation to render 3-D promotional movies. Which of the following is the most important component?
A large company is changing its password length requirements. The Chief Information Officer is mandating that passwords now be at least 12 characters long, instead of 10. Which of the following should be used to adjust this setting?
Group Policy
Which of the following environments allows for the testing of critical systems without the risk of them being negatively impacted by changes?
An office is experiencing constant connection attempts to the corporate Wi-Fi. Which of the following should be disabled to mitigate connection attempts?
SSID
Which of the following involves sending arbitrary characters in a web page request?
Which of the following operating systems would most likely be used to run the inventory management system at a factory?
Which of the following does MFA provide?
A branch office suspects a machine contains ransomware. Which of the following mitigation steps should a technician take first?
A technician downloaded a software program to a network share. When the technician attempts to copy the program to the Windows tablet for installation, the technician receives an error. Which of the following is the best procedure for the technician to use to complete the assignment?
Copy the program file to a USB drive and install.
Which of the following is the best way to limit the loss of confidential data if an employee's company smartphone is lost or stolen?
A laptop that was in the evidence room of a police station is missing. Which of the following is the best reason to refer to chain of custody documentation?
Which of the following Windows 10 editions is the most appropriate for a single user who wants to encrypt a hard drive with BitLocker?
A company-owned mobile device is displaying a high number of ads, receiving data-usage limit notifications, and experiencing slow response. After checking the device, a technician notices the device has been jailbroken. Which of the following should the technician do next?
A technician needs to perform after-hours service starting at 10:00 p.m. The technician is currently 20 minutes late. The customer will also be late. Which of the following should the technician do considering proper communication techniques and professionalism?
Do not notify the customer if arriving before the customer.
A user reports seeing random, seemingly non-malicious advertisement notifications in the Windows 10 Action Center. The notifications indicate the advertisements are coming from a web browser. Which of the following is the best solution for a technician to implement?
A technician is modifying the default home page of all the workstations in a company. Which of the following will help to implement this change?
A technician has identified malicious traffic originating from a user's computer. Which of the following is the best way to identify the source of the attack?
Which of the following is command options is used to display hidden files and directories?
A client wants a technician to set up a proxy server in a branch office to manage internet access. This involves configuring the workstations to use the new proxy server. Which of the following Internet Options tabs in Control Panel would be most appropriate for the technician to use to configure the settings?
A technician is troubleshooting a PC because the user has reported strange pop-up windows and computer performance issues. Which of the following actions should the technician take next?
A user reports a hardware issue to the help desk. Which of the following should the help desk technician do first when responding to the user?
A technician is hardening a company file server and needs to prevent unauthorized LAN devices from accessing stored files. Which of the following should the technician use?
A large organization is researching proprietary software with vendor support for a multiuser environment. Which of the following EULA types should be selected?
A technician is unable to completely start up a system. The OS freezes when the desktop background appears, and the issue persists when the system is restarted. Which of the following should the technician do next to troubleshoot the issue?
A user's laptop has been performing slowly and redirecting to unfamiliar websites. The user has also noticed random pop-up windows. Which of the following is the first step a technician should take to resolve the issue?
Which of the following filesystems replaced FAT as the preferred filesystem for Microsoft Windows OS?
Which of the following file extensions should a technician use for a PowerShell script?
A student is setting up a new Windows 10 laptop for the upcoming semester. The student is interested in customizing the wallpaper. Which of the following should the student use to change the wallpaper?
A technician needs to replace a PC's motherboard. The technician shuts down the PC. Which of the following steps should the technician take next?
A company wants to remove information from past users' hard drives in order to reuse the hard drives Witch of the following is the MOST secure method
A user has requested help setting up the fingerprint reader on a Windows 10 laptop. The laptop is equipped with a fingerprint reader and is joined to a domain Group Policy enables Windows Hello on all computers in the environment. Which of the following options describes how to set up Windows Hello Fingerprint for the user?
A user wants to set up speech recognition on a PC. In which of the following Windows Settings tools can the user enable this option?
A user receives a notification indicating the antivirus protection on a company laptop is out of date. A technician is able to ping the user's laptop. The technician checks the antivirus parent servers and sees the latest signatures have been installed. The technician then checks the user's laptop and finds the antivirus engine and definitions are current. Which of the following has MOST likely occurred?
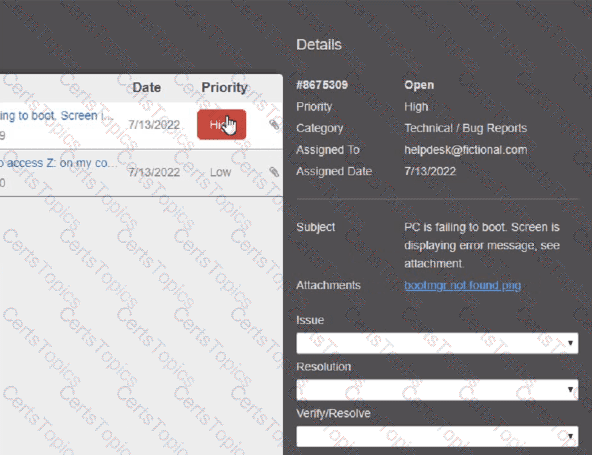
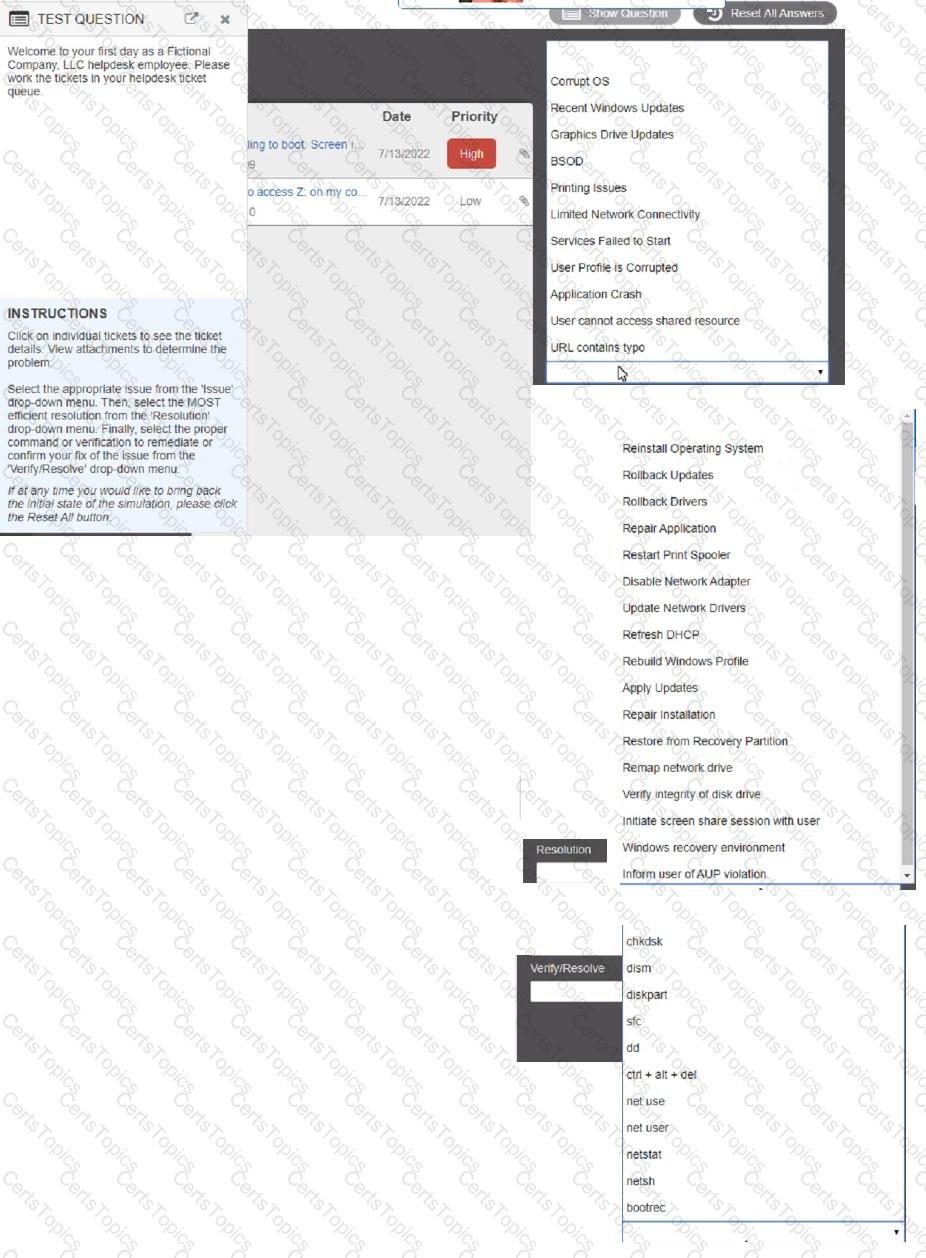
Welcome to your first day as a Fictional Company. LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
Click on individual tickers to see the ticket details. View attachments to determine the problem.
Select the appropriate issue from the 'issue' drop-down menu. Then, select the MOST efficient resolution from the 'Resolution' drop-down menu. Finally, select the proper command or verification to remediate or confirm your fix of the issue from the Verify Resolve drop-down menu.
A user is unable to log in to the domain with a desktop PC, but a laptop PC is working properly on the same network. A technician logs in lo the desktop PC with a local account but is unable to browse to the secure intranet site to get troubleshooting tools. Which of the following is the MOST likely cause of the issue?
A technician needs to document who had possession of evidence at every step of the process. Which of the following does this process describe?
As part of a CYOD policy a systems administrator needs to configure each user's Windows device to require a password when resuming from a period of sleep or inactivity. Which of the following paths will lead the administrator to the correct settings?
A technician is investigating an employee's smartphone that has the following symptoms
• The device is hot even when it is not in use.
•Applications crash, especially when others are launched.
• Certain applications, such as GPS, are in portrait mode when they should be in landscape mode.
Which of the following can the technician do to MOST likely resolve these issues with minimal impact? (Select TWO).
A user corrects a laptop that is running Windows 10 to a docking station with external monitors when working at a desk. The user would like to close the laptop when it is docked, but the user reports it goes to sleep when it is closed. Which of the following is the BEST solution to prevent the laptop from going to sleep when it is closed and on the docking station?
A user is experiencing frequent malware symptoms on a Windows workstation. The user has tried several times to roll back the state but the malware persists. Which of the following would MOST likely resolve the issue?
A user reports a PC is running slowly. The technician suspects it has a badly fragmented hard drive. Which of the following tools should the technician use?
Which of the following Linux commands would be used to install an application?
Upon downloading a new ISO, an administrator is presented with the following string:
59d15a16ce90cBcc97fa7c211b767aB
Which of the following BEST describes the purpose of this string?
A user calls the help desk to report potential malware on a computer. The anomalous activity began after the user clicked a link to a free gift card in a recent email The technician asks the user to describe any unusual activity, such as slow performance, excessive pop-ups, and browser redirections. Which of the following should the technician do NEXT?
A user is configuring a new SOHO Wi-Fi router for the first time. Which of the following settings should the user change FIRST?
A technician is troubleshooting an issue involving programs on a Windows 10 machine that are loading on startup but causing excessive boot times. Which of the following should the technician do to selectively prevent programs from loading?
A user reports that antivirus software indicates a computer is infected with viruses. The user thinks this happened white browsing the internet. The technician does not recognize the interface with which the antivirus message is presented. Which of the following is the NEXT step the technician should take?
A technician needs to interconnect two offices to the main branch while complying with good practices and security standards. Which of the following should the technician implement?
A change advisory board just approved a change request. Which of the following is the MOST likely next step in the change process?
A wireless network is set up, but it is experiencing some interference from other nearby SSIDs. Which of the following can BEST resolve the interference?
A user's smartphone data usage is well above average. The user suspects an installed application is transmitting data in the background. The user would like to be alerted when an application attempts to communicate with the internet. Which of the following BEST addresses the user's concern?
An Android user contacts the help desk because a company smartphone failed to complete a tethered OS update A technician determines there are no error messages on the device Which of the following should the technician do NEXT?
A user reports that a PC seems to be running more slowly than usual. A technician checks system resources, but disk, CPU, and memory usage seem to be fine. The technician sees that GPU temperature is extremely high. Which of the following types of malware is MOST likely to blame?
A technician found that an employee is mining cryptocurrency on a work desktop. The company has decided that this action violates its guidelines. Which of the following should be updated to reflect this new requirement?
Which of the following is the MOST important environmental concern inside a data center?
An architecture firm is considering upgrading its computer-aided design (CAD) software to the newest version that forces storage of backups of all CAD files on the software's cloud server. Which of the following is MOST likely to be of concern to the IT manager?
Someone who is fraudulently claiming to be from a reputable bank calls a company employee. Which of the following describes this incident?
A company is Issuing smartphones to employees and needs to ensure data is secure if the devices are lost or stolen. Which of the following provides the BEST solution?
A systems administrator is setting up a Windows computer for a new user Corporate policy requires a least privilege environment. The user will need to access advanced features and configuration settings for several applications. Which of the following BEST describes the account access level the user will need?
Which of the following OS types provides a lightweight option for workstations thai need an easy-to-use browser-based interface?
Welcome to your first day as a Fictional Company. LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
Click on individual tickers to see the ticket details. View attachments to determine the problem.
Select the appropriate issue from the 'issue' drop-down menu. Then, select the MOST efficient resolution from the 'Resolution' drop-down menu. Finally, select the proper command or verification to remediate or confirm your fix of the issue from the Verify Resolve drop-down menu.
A user attempts to open some files, but a message appears stating that the files are encrypted. The user was able to access these files before without receiving this message and no changes have been made within the company. Which of the following has infected the computer?
A user reports that a workstation is operating sluggishly Several other users operate on the same workstation and have reported that the workstation is operating normally. The systems administrator has validated that the workstation functions normally. Which of the following steps should the systems administrator most likely attempt NEXT?
A technician is installing new network equipment in a SOHO and wants to ensure the equipment is secured against external threats on the Internet. Which of the following actions should the technician do FIRST?
The network was breached over the weekend System logs indicate that a single user's account was successfully breached after 500 attempts with a dictionary attack. Which of the following would BEST mitigate this threat?
A desktop specialist needs to prepare a laptop running Windows 10 for a newly hired employee. Which of the following methods should the technician use to refresh the laptop?
A change advisory board authorized a setting change so a technician is permitted to implement the change. The technician successfully implemented the change. Which of the following should be done NEXT?
A user tries to access commonly used web pages but is redirected to unexpected websites. Clearing the web browser cache does not resolve the issue. Which of the following should a technician investigate NEXT to resolve the issue?
A Windows user recently replaced a computer The user can access the public internet on the computer; however, an internal site at https7/companyintranet.com:8888 is no longer loading. Which of the following should a technician adjust to resolve the issue?
A technician receives a call (rom a user who is having issues with an application. To best understand the issue, the technician simultaneously views the user's screen with the user. Which of the following would BEST accomplish this task?
A user updates a mobile device's OS. A frequently used application becomes consistently unresponsive immediately after the device is launched. Which of the following troubleshooting steps should the user perform FIRST?
A technician installed Windows 10 on a workstation. The workstation only has 3.5GB of usable RAM, even though the technician installed 8GB. Which of the following is the MOST likely reason this system is not utilizing all the available RAM?
A technician needs to add an individual as a local administrator on a Windows home PC. Which of the following utilities would the technician MOST likely use?
A customer calls a service support center and begins yelling at a technician about a feature for a product that is not working to the customer's satisfaction. This feature is not supported by the service support center and requires a field technician to troubleshoot. The customer continues to demand service. Which of the following is the BEST course of action for the support center representative to take?
A user added a second monitor and wants to extend the display to it. In which of the following Windows settings will the user MOST likely be able to make this change?
A technician is securing a new Windows 10 workstation and wants to enable a Screensaver lock. Which of the following options in the Windows settings should the technician use?
A user's corporate phone was stolen, and the device contains company trade secrets. Which of the following technologies should be implemented to mitigate this risk? (Select TWO).
A technician is working on a way to register all employee badges and associated computer IDs. Which of the following options should the technician use in order to achieve this objective?
A company implemented a BYOD policy and would like to reduce data disclosure caused by malware that may infect these devices. Which of the following should the company deploy to address these concerns?
Which of the following is used to explain issues that may occur during a change implementation?
Which of the following features allows a technician to configure policies in a Windows 10 Professional desktop?
Which of the following default system tools can be used in macOS to allow the technician to view the screen simultaneously with the user?
A kiosk, which is running Microsoft Windows 10, relies exclusively on a numeric keypad to allow customers to enter their ticket numbers but no other information. If the kiosk is idle for four hours, the login screen locks. Which of the following sign-on options would allow any employee the ability to unlock the kiosk?
Which of the following script types is used with the Python language by default?
A technician is setting up a conference room computer with a script that boots the application on login. Which of the following would the technician use to accomplish this task? (Select TWO).
Which of the following would MOST likely be deployed to enhance physical security for a building? (Select TWO).
A user receives an error message from an online banking site that states the following:
Your connection is not private. Authority invalid.
Which of the following actions should the user take NEXT?
A technician is troubleshooting a mobile device that was dropped. The technician finds that the screen (ails to rotate, even though the settings are correctly applied. Which of the following pieces of hardware should the technician replace to resolve the issue?
A Windows workstation that was recently updated with approved system patches shut down instead of restarting. Upon reboot, the technician notices an alert stating the workstation has malware in the root OS folder. The technician promptly performs a System Restore and reboots the workstation, but the malware is still detected. Which of the following BEST describes why the system still has malware?
A manager called the help desk to ask for assistance with creating a more secure environment for the finance department- which resides in a non-domain environment. Which of the following would be the BEST method to protect against unauthorized use?
A technician is in the process of installing a new hard drive on a server but is called away to another task. The drive has been unpackaged and left on a desk. Which of the following should the technician perform before leaving?
A user receives the following error while attempting to boot a computer.
BOOTMGR is missing
press Ctrl+Alt+Del to restart
Which of the following should a desktop engineer attempt FIRST to address this issue?
Which of the following is MOST likely used to run .vbs files on Windows devices?
A technician downloads a validated security tool and notes the vendor hash of a58e87a2. When the download is complete, the technician again validates the hash, but the value returns as 2a876a7d3. Which of the following is the MOST likely cause of the issue?
Which of the following options should MOST likely be considered when preserving data from a hard drive for forensic analysis? (Select TWO).
A technician is troubleshooting a PC that has been performing poorly. Looking at the Task Manager, the technician sees that CPU and memory resources seem fine, but disk throughput is at 100%.
Which of the following types of malware is the system MOST likely infected with?
An IT security team is implementing a new Group Policy that will return a computer to the login after three minutes. Which of the following BEST describes the change in policy?
A user notices a small USB drive is attached to the user's computer after a new vendor visited the office. The technician notices two files named grabber.exe and output.txt. Which of the following attacks is MOST likely occurring?
Which of the following is the default GUI and file manager in macOS?
A company needs employees who work remotely to have secure access to the corporate intranet. Which of the following should the company implement?
Which of the following is used to integrate Linux servers and desktops into Windows Active Directory environments?
A user is trying to use a third-party USB adapter but is experiencing connection issues. Which of the following tools should the technician use to resolve this issue?
A technician receives a call from a user who is unable to open Outlook. The user states that Outlook worked fine yesterday, but the computer may have restarted sometime overnight. Which of the following is the MOST likely reason Outlook has stopped functioning?
Which of the following is a consequence of end-of-lite operating systems?
Sensitive data was leaked from a user's smartphone. A technician discovered an unapproved application was installed, and the user has full access to the device's command shell. Which of the following is the NEXT step the technician should take to find the cause of the leaked data?
A technician is reimaging a desktop PC. The technician connects the PC to the network and powers it on. The technician attempts to boot the computer via the NIC to image the computer, but this method does not work. Which of the following is the MOST likely reason the computer is unable to boot into the imaging system via the network?
A technician has just used an anti-malware removal tool to resolve a user's malware issue on a corporate laptop. Which of the following BEST describes what the technician should do before returning the laptop to the user?
Before leaving work, a user wants to see the traffic conditions for the commute home. Which of the following tools can the user employ to schedule the browser to automatically launch a traffic website at 4:45 p.m.?
Which of the following is the STRONGEST wireless configuration?
Which of the following data is MOST likely to be regulated?
A technician is working to resolve a Wi-Fi network issue at a doctor's office that is located next to an apartment complex. The technician discovers that employees and patients are not the only people on the network. Which of the following should the technician do to BEST minimize this issue?
An analyst needs GUI access to server software running on a macOS server. Which of the following options provides the BEST way for the analyst to access the macOS server from the Windows workstation?
Which of the following is the MOST basic version of Windows that includes BitLocker?
A team of support agents will be using their workstations to store credit card data. Which of the following should the IT department enable on the workstations in order to remain compliant with common regulatory controls? (Select TWO).
A field technician applied a Group Policy setting to all the workstations in the network. This setting forced the workstations to use a specific SNTP server. Users are unable to log in now. Which of the following is the MOST likely cause of this issue?
A police officer often leaves a workstation for several minutes at a time. Which of the following is the BEST way the officer can secure the workstation quickly when walking away?
A mobile phone user has downloaded a new payment application that allows payments to be made with a mobile device. The user attempts to use the device at a payment terminal but is unable to do so successfully. The user contacts a help desk technician to report the issue. Which of the following should the technician confirm NEXT as part of the troubleshooting process?
A call center handles inquiries into billing issues for multiple medical facilities. A security analyst notices that call center agents often walk away from their workstations, leaving patient data visible for anyone to see. Which of the following should a network administrator do to BEST prevent data theft within the call center?
A user's system is infected with malware. A technician updates the anti-malware software and runs a scan that removes the malware. After the user reboots the system, it once again becomes infected with malware. Which of the following will MOST likely help to permanently remove the malware?
A junior administrator is responsible for deploying software to a large group of computers in an organization. The administrator finds a script on a popular coding website to automate this distribution but does not understand the scripting language. Which of the following BEST describes the risks in running this script?
A technician just completed a Windows 10 installation on a PC that has a total of 16GB of RAM. The technician notices the Windows OS has only 4GB of RAM available for use. Which of the following explains why the OS can only access 46B of RAM?
Which of the following is MOST likely contained in an EULA?
The web browsing speed on a customer's mobile phone slows down every few weeks and then returns to normal after three or four days. Restarting the device does not usually restore performance. Which of the following should a technician check FIRST to troubleshoot this issue?
A user has a license for an application that is in use on a personal home laptop. The user approaches a systems administrator about using the same license on
multiple computers on the corporate network. Which of the following BEST describes what the systems administrator should tell the user?
A technician needs to manually set an IP address on a computer that is running macOS. Which of the following commands should the technician use?
A systems administrator needs to reset a users password because the user forgot it. The systems administrator creates the new password and wants to further protect the user's account Which of the following should the systems administrator do?
A help desk technician runs the following script: Inventory.py. The technician receives the following error message:
How do you want to Open this file?
Which of the following is the MOST likely reason this script is unable to run?
In which of the following scenarios would remote wipe capabilities MOST likely be used? (Select TWO).
Which of the following command-line tools will delete a directory?
A user reports a workstation has been performing strangely after a suspicious email was opened on it earlier in the week. Which of the following should the technician perform FIRST?
A user in a corporate office reports the inability to connect to any network drives. No other users have reported this issue. Which of the following is the MOST likely reason the user is having this issue?
A user calls the help desk and reports a workstation is infected with malicious software. Which of the following tools should the help desk technician use to remove the malicious software? (Select TWO).
A manager reports that staff members often forget the passwords to their mobile devices and applications. Which of the following should the systems administrator do to reduce the number of help desk tickets submitted?
A user reports a PC is running slowly. The technician suspects high disk I/O. Which of the following should the technician perform NEXT?