Huawei Related Exams
H12-891_V1.0 Exam







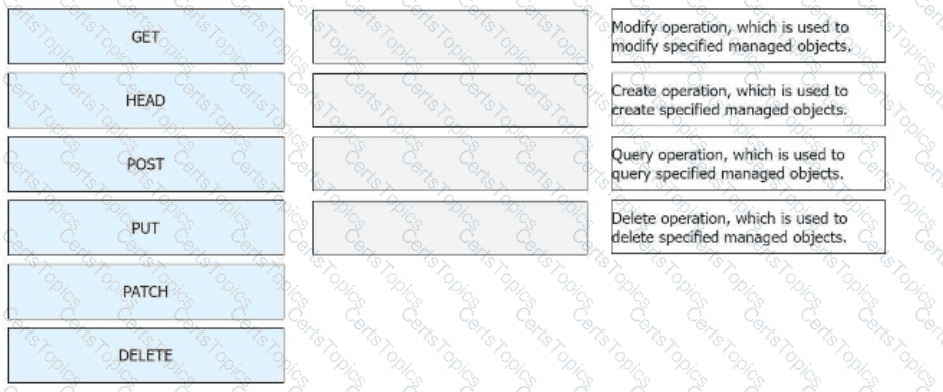
Huawei Open Programmability System (OPS) uses HTTP methods to access managed objects to manage network devices. Drag the HTTP methods to their corresponding functions.
Which of the following statements is correct about the differences between NSR and NSF?
On a VXLAN-based virtualized network, if the fabric networking mode is centralized gateway networking, the gateway is located on the _____ device. (Capitalize the first letter.)