EMC Related Exams
D-ISM-FN-23 Exam







Refer to the Exhibit:
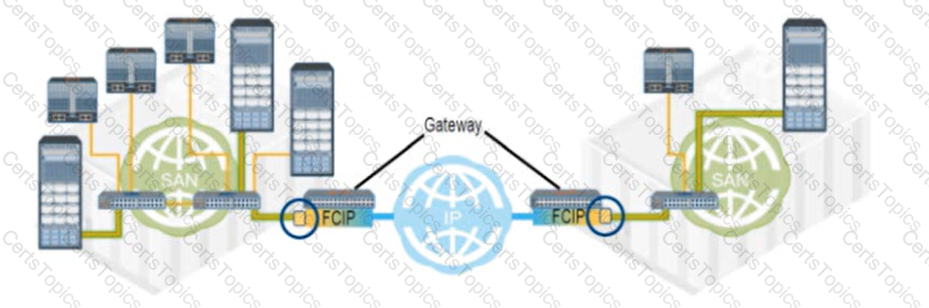
What type of FC port connects each FCIP gateway to each FC SAN?
A Fibre Channel switch has eight ports and all ports must be operational from 8 AM to 8 PM, Monday through Friday. However, a failure of Port 2 occurs on a particular week as follows:
Monday = 10 AM to 12 PM Wednesday = 4 PM to 9 PM Thursday = 4 PM to 7 PM
Friday = 3 PM to 6 PM Saturday = 9 AM to 1 PM
What is the availability of Port 2 in that week?
Which block storage device protocol achieves the optimal cost-effective balance between I/O performance and high storage capacity for midrange storage applications?