Scenario 8: Biotide is a pharmaceutical company that produces medication for treating different kinds of diseases. The company was founded in 1997, and since then it has contributed in solving some of the most challenging healthcare issues.
As a pharmaceutical company, Biotide operates in an environment associated with complex risks. As such, the company focuses on risk management strategies that ensure the effective management of risks to develop high-quality medication. With the large amount of sensitive information generated from the company, managing information security risks is certainly an important part of the overall risk management process. Biotide utilizes a publicly available methodology for conducting risk assessment related to information assets. This methodology helps Biotide to perform risk assessment by taking into account its objectives and mission. Following this method, the risk management process is organized into four activity areas, each of them involving a set of activities, as provided below.
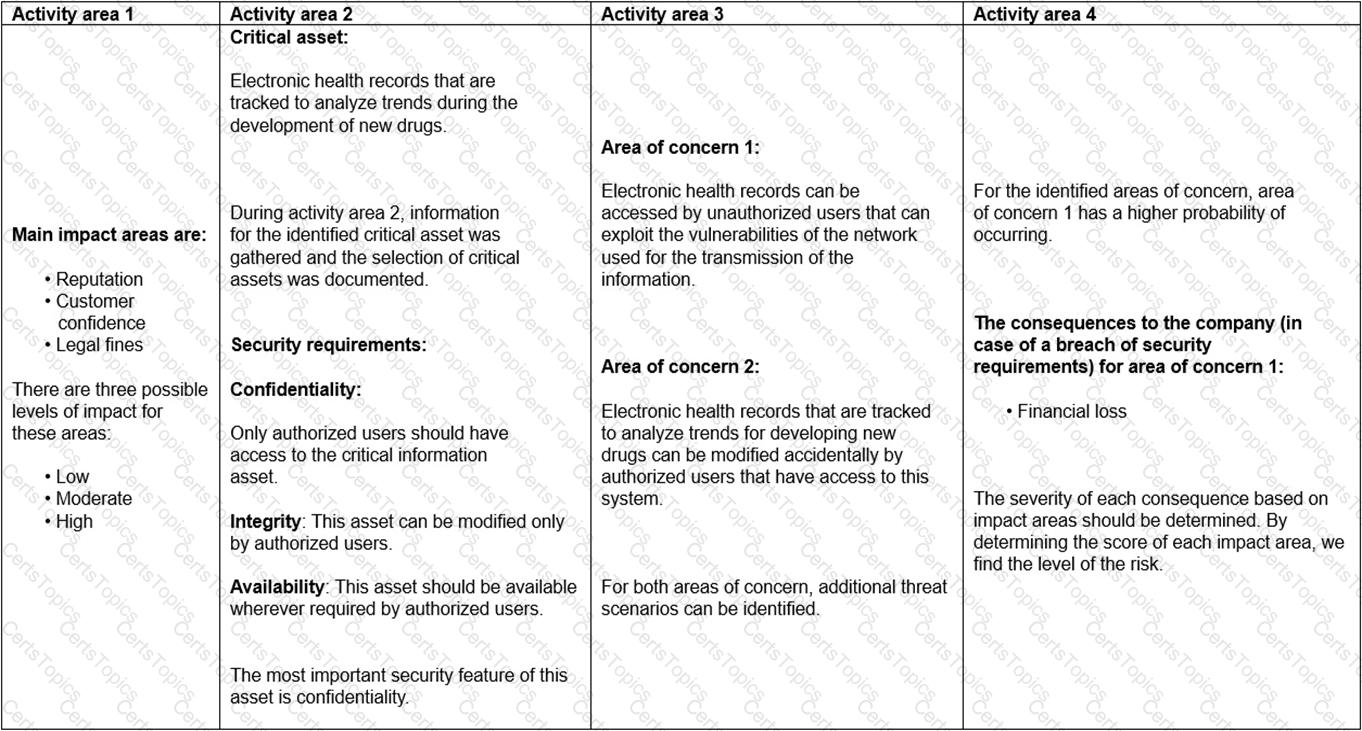
1. Activity area 1: The organization determines the criteria against which the effects of a risk occurring can be evaluated. In addition, the impacts of risks are also defined.
2. Activity area 2: The purpose of the second activity area is to create information asset profiles. The organization identifies critical information assets, their owners, as well as the security requirements for those assets. After determining the security requirements, the organization prioritizes them. In addition, the organization identifies the systems that store, transmit, or process information.
3. Activity area 3: The organization identifies the areas of concern which initiates the risk identification process. In addition, the organization analyzes and determines the probability of the occurrence of possible threat scenarios.
4. Activity area 4: The organization identifies and evaluates the risks. In addition, the criteria specified in activity area 1 is reviewed and the consequences of the areas of concerns are evaluated. Lastly, the level of identified risks is determined.
The table below provides an example of how Biotide assesses the risks related to its information assets following this methodology:
Based on the scenario above, answer the following question:
Which risk assessment methodology does Biotide use?
Scenario 4: In 2017, seeing that millions of people turned to online shopping, Ed and James Cordon founded the online marketplace for footwear called Poshoe. In the past, purchasing pre-owned designer shoes online was not a pleasant experience because of unattractive pictures and an inability to ascertain the products’ authenticity. However, after Poshoe’s establishment, each product was well advertised and certified as authentic before being offered to clients. This increased the customers’ confidence and trust in Poshoe’s products and services. Poshoe has approximately four million users and its mission is to dominate the second-hand sneaker market and become a multi-billion dollar company.
Due to the significant increase of daily online buyers, Poshoe’s top management decided to adopt a big data analytics tool that could help the company effectively handle, store, and analyze data. Before initiating the implementation process, they decided to conduct a risk assessment. Initially, the company identified its assets, threats, and vulnerabilities associated with its information systems. In terms of assets, the company identified the information that was vital to the achievement of the organization’s mission and objectives. During this phase, the company also detected a rootkit in their software, through which an attacker could remotely access Poshoe’s systems and acquire sensitive data.
The company discovered that the rootkit had been installed by an attacker who had gained administrator access. As a result, the attacker was able to obtain the customers’ personal data after they purchased a product from Poshoe. Luckily, the company was able to execute some scans from the target device and gain greater visibility into their software’s settings in order to identify the vulnerability of the system.
The company initially used the qualitative risk analysis technique to assess the consequences and the likelihood and to determine the level of risk. The company defined the likelihood of risk as “a few times in two years with the probability of 1 to 3 times per year.” Later, it was decided that they would use a quantitative risk analysis methodology since it would provide additional information on this major risk. Lastly, the top management decided to treat the risk immediately as it could expose the company to other issues. In addition, it was communicated to their employees that they should update, secure, and back up Poshoe’s software in order to protect customers’ personal information and prevent unauthorized access from attackers.
According to scenario 4, the top management of Poshoe decided to treat the risk immediately after conducting the risk analysis. Is this in compliance with risk management best practices?
What are opportunities?
Based on NIST Risk Management Framework, what is the last step of a risk management process?