Verified By IT Certified Experts
CertsTopics.com Certified Safe Files
Up-To-Date Exam Study Material
99.5% High Success Pass Rate
100% Accurate Answers
Instant Downloads
Exam Questions And Answers PDF
Try Demo Before You Buy






Which statements about a Distributed Version Control System are correct?Choose 2 answers
Which enables you to use artifacts from a completed build In the workspace of the currently running build?
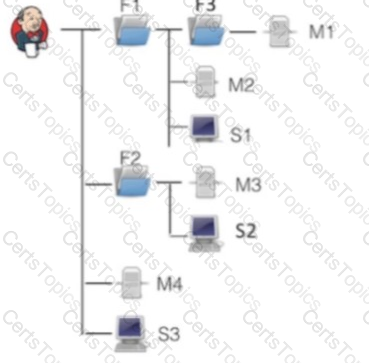
You have an Operations Center architecture as pictured in the exhibit above, where there are:
• Three folders: F1, F2, and F3
• Three shared agents: SI, S2, and S3
• Four client masters: Ml, M2, M3, and M4
Which statements are true?
Choose 2 answers