Cisco Related Exams
200-201 Exam







The Cisco 200-201 exam, also known as the Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS) exam, is ideal for individuals seeking to:
The Cisco 200-201 exam focuses on core security areas, including:
CertsTopics offers a variety of high-quality study materials for the CyberOps Associate Certification Exam, including 200-201 PDFs and testing engine. Our 200-201 preparation materials are designed to mirror the exam’s format, giving you a real exam experience.
A malicious file has been identified in a sandbox analysis tool.
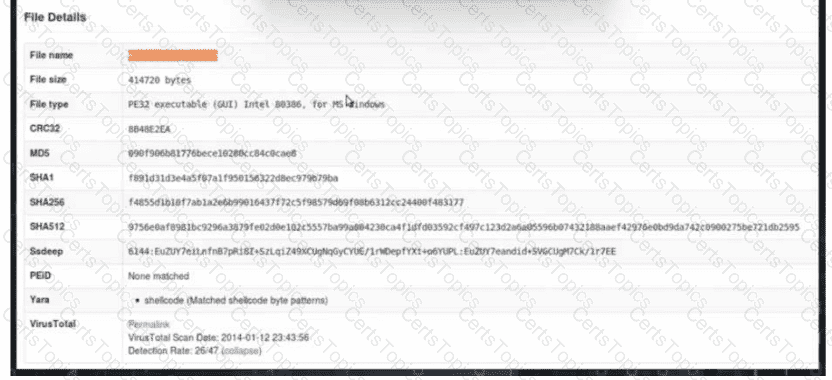
Which piece of information is needed to search for additional downloads of this file by other hosts?
Which attack method is being used when an attacker tries to compromise a network with an authentication system that uses only 4-digit numeric passwords and no username?
During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?