A developer runs an application that displays scores for sports games on Amazon EC2 instances. The application uses a Redis client to retrieve the scores from an Amazon ElastiCache (Redis OSS) cluster.
The developer observes increased latency during operations on the cache because of connection failures to the cluster. The developer needs to resolve the latency issues.
A developer is creating an AWS Lambda function that consumes messages from an Amazon Simple Queue Service (Amazon SQS) standard queue. The developer notices that the Lambda function processes some messages multiple times.
How should developer resolve this issue MOST cost-effectively?
A company requires that all applications running on Amazon EC2 use 1AM roles to gam access to AWS services. A developer is modifying an application that currently relies on 1AM user access keys stored in environment variables to access Amazon DynamoDB tables using boto, the AWS SDK for Python.
The developer associated a role with the same permissions as the 1AM user to the EC2 instance, then deleted the 1AM user. When the application was restarted, the AWS
Access Denied Exception messages started appearing in the application logs. The developer was able to use their personal account on the server to run DynamoDB API commands using the AWS CLI.
What is the MOST likely cause of the exception?
A gaming application stores scores for players in an Amazon DynamoDB table that has four attributes: user_id, user_name, user_score, and user_rank. The users are allowed to update their names only. A user is authenticated by web identity federation.
Which set of conditions should be added in the policy attached to the role for the dynamodb:PutItem API call?
A company uses AWS CloudFormation to deploy an application that includes an Amazon API Gateway REST API integrated with AWS Lambda and Amazon DynamoDB. The application has three stages: development, testing, and production, each with its own DynamoDB table.
The company wants to deploy a new production release and route 20% of traffic to the new version while keeping 80% of traffic on the existing production version. The solution must minimize the number of errors that any single customer experiences.
Which approach should the developer take?
A developer is building an ecommerce application that uses AWS Lambda functions. Each Lambda function performs a specific step in a customer order workflow, such as order processing and inventory management. The developer must ensure that the Lambda functions run in a specific order.
Which solution will meet this requirement with the LEAST operational overhead?
A company is developing a new ecommerce platform on AWS. The company wants to implement an event-driven architecture for the company’s order processing system. The system must perform the following steps when a customer places an order:
Update inventory in the company’s warehouse management system
Send a confirmation email message to the customer
Notify the company’s shipping department to prepare the customer’s package
Update the customer’s order history
A developer wants to ensure loose coupling between services so that the company can easily add new steps in the future. Which solution will meet these requirements?
A company has an application that generates large binary data outside of AWS . The company must encrypt the data before uploading the data to an Amazon S3 bucket.
Which solution will meet this requirement?
A developer is creating an application that must transfer expired items from Amazon DynamoDB to Amazon S3. The developer sets up the DynamoDB table to automatically delete items after a specific TTL. The application must process the items in DynamoDB and then must store the expired items in Amazon S3. The entire process, including item processing and storage in Amazon S3, will take 5 minutes.
Which solution will meet these requirements with the LEAST operational overhead?
A company has implemented a pipeline in AWS CodePipeline. The company Is using a single AWS account and does not use AWS Organizations. The company needs to test its AWS CloudFormation templates in its primary AWS Region and a disaster recovery Region.
Which solution will meet these requirements with the MOST operational efficiency?
A company uses an AWS Lambda function to transfer files from an Amazon S3 bucket to the company ' s SFTP server. The Lambda function connects to the SFTP server by using credentials such as username and password. The company uses Lambda environment variables to store these credentials.
A developer needs to implement encrypted username and password credentials.
Which solution will meet these requirements?
A developer is managing an application that uploads user files to an Amazon S3 bucket named companybucket. The company wants to maintain copies of all the files uploaded by users for compliance purposes, while ensuring users still have access to the data through the application.
Which IAM permissions should be applied to users to ensure they can create but not remove files from the bucket?
A company uses AWS Secrets Manager to store API keys for external REST services. The company uses an AWS Lambda function to rotate the API keys on a regular schedule.
Due to an error in the Lambda function, the API keys are successfully updated in AWS Secrets Manager but are not updated in the external REST services. Before investigating the root cause of the issue, the company wants to resume requests to the external REST services as quickly as possible.
Which solution will meet this requirement with the LEAST operational overhead ?
A company is developing a web application that allows its employees to upload a profile picture to a private Amazon S3 bucket. There is no size limit for the profile pictures, which should be displayed every time an employee logs in. For security reasons, the pictures cannot be publicly accessible.
What is a viable long-term solution for this scenario?
A social media application stores millions of video clips in Amazon S3 and serves them to users worldwide. Traffic is highly variable and can spike to more than 10,000 PUT and GET requests per second . Users report poor video streaming quality .
Which solution will provide the LARGEST improvement in performance ?
A company is creating a new application that gives users the ability to upload and share short video files. The average size of the video files is 10 MB. After a user uploads a file, a message needs to be placed into an Amazon Simple Queue Service (Amazon SQS) queue so the file can be processed. The files need to be accessible for processing within 5 minutes.
Which solution will meet these requirements MOST cost-effectively?
A developer is migrating an application to Amazon Elastic Kubernetes Service (Amazon EKS). The developer migrates the application to Amazon Elastic Container Registry (Amazon ECR) with an EKS cluster.
As part of the application migration to a new backend, the developer creates a new AWS account. The developer makes configuration changes to the application to point the application to the new AWS account and to use new backend resources. The developer successfully tests the changes within the application by deploying the pipeline.
The Docker image build and the pipeline deployment are successful, but the application is still connecting to the old backend. The developer finds that the application ' s configuration is still referencing the original EKS cluster and not referencing the new backend resources.
Which reason can explain why the application is not connecting to the new resources?
A food-delivery company has an application that uses an Amazon DynamoDB table for customer orders. The table is in on-demand mode. The table uses order_date as the partition key. The table uses a combination of customer_id and order_id as the sort key (customer_id#order_id). During peak order periods, write operations to the table are being throttled. What should a developer do to resolve this issue?
A development team maintains a web application by using a single AWS CloudFormation template. The template defines web servers and an Amazon RDS database. The team uses the Cloud Formation template to deploy the Cloud Formation stack to different environments.
During a recent application deployment, a developer caused the primary development database to be dropped and recreated. The result of this incident was a loss of data. The team needs to avoid accidental database deletion in the future.
Which solutions will meet these requirements? (Choose two.)
A company has built an AWS Lambda function to convert large image files into output files that can be used in a third-party viewer application The company recently added a new module to the function to improve the output of the generated files However, the new module has increased the bundle size and has increased the time that is needed to deploy changes to the function code.
How can a developer increase the speed of the Lambda function deployment?
A company has a large amount of data in an Amazon DynamoDB table. A large batch of data is appended to the table once each day. The company wants a solution that will make all the existing and future data in DynamoDB available for analytics on a long-term basis.
Which solution meets these requirements with the LEAST operational overhead?
An ecommerce company is developing a serverless application to track user activities. The company needs to track each type of activity with a timestamp and a unique product ID. The company also must track actions that are associated with each activity, such as product views, shopping cart actions, purchases, and checkout processes.
The company is planning a marketing campaign based on each user ' s activity. A developer needs to implement a partitioning strategy for an Amazon DynamoDB table to meet the data storage and access requirements for the application. The strategy must maximize provisioned throughput efficiency while minimizing the risk of throttling.
Which solution will meet these requirements?
A developer has an application that is composed of many different AWS Lambda functions. The Lambda functions all use some of the same dependencies. To avoid security issues the developer is constantly updating the dependencies of all of the Lambda functions. The result is duplicated effort to reach function.
How can the developer keep the dependencies of the Lambda functions up to date with the LEAST additional complexity?
An ecommerce company has an integration with a payment processing service that publishes messages about payment activities to an Amazon SNS topic. A developer is building an AWS Lambda function to process payment refunds from the SNS topic. The Lambda function must process only messages related to refunds. Which solution will meet this requirement in the MOST operationally efficient way?
A developer is creating an AWS Lambda function that needs network access to private resources in a VPC.
A company is building a micro services app1 cation that consists of many AWS Lambda functions. The development team wants to use AWS Serverless Application Model (AWS SAM) templates to automatically test the Lambda functions. The development team plans to test a small percentage of traffic that is directed to new updates before the team commits to a full deployment of the application.
Which combination of steps will meet these requirements in the MOST operationally efficient way? (Select TWO.)
A company has an ecommerce application. To track product reviews, the company ' s development team uses an Amazon DynamoDB table.
Every record includes the following
• A Review ID a 16-digrt universally unique identifier (UUID)
• A Product ID and User ID 16 digit UUlDs that reference other tables
• A Product Rating on a scale of 1-5
• An optional comment from the user
The table partition key is the Review ID. The most performed query against the table is to find the 10 reviews with the highest rating for a given product.
Which index will provide the FASTEST response for this query " ?
A company stores its data in data tables in a series of Amazon S3 buckets. The company received an alert that customer credit card information might have been exposed in a data table on one of the company ' s public applications. A developer needs to identify all potential exposures within the application environment.
Which solution will meet these requirements?
A developer is migrating some features from a legacy monolithic application to use AWS Lambda functions instead. The application currently stores data in an Amazon Aurora DB cluster that runs in private subnets in a VPC. The AWS account has one VPC deployed. The Lambda functions and the DB cluster are deployed in the same AWS Region in the same AWS account.
The developer needs to ensure that the Lambda functions can securely access the DB cluster without crossing the public internet.
Which solution will meet these requirements?
A company ' s development team uses an SSH key pair to copy files among a large fleet of development servers. The SSH key pair has been compromised. A developer has generated a replacement key pair. The company has deployed the AWS Systems Manager Agent (SSM Agent) and the Amazon CloudWatch agent on all of the development servers.
The developer needs a solution to distribute the new key to all the Linux servers.
Which solution will meet these requirements in the MOST operationally efficient way?
A company is using AWS SAM to develop a social media application. A developer needs a quick way to test AWS Lambda functions locally by using test event payloads. The developer needs the structure of these test event payloads to match the actual events that AWS services create.
Which solution will meet these requirements with the LEAST development effort?
A developer is writing a serverless application that requires an AWS Lambda function to be invoked every 10 minutes.
What is an automated and serverless way to invoke the function?
A company runs an ecommerce application on AWS. The application stores data in an Amazon Aurora database.
A developer is adding a caching layer to the application. The caching strategy must ensure that the application always uses the most recent value for each data item.
Which caching strategy will meet these requirements?
A company has a website that displays a daily newsletter. When a user visits the website, an AWS Lambda function processes the browser ' s request and queries the company ' s on-premises database to obtain the current newsletter. The newsletters are stored in English. The Lambda function uses the Amazon Translate TranslateText API operation to translate the newsletters, and the translation is displayed to the user.
Due to an increase in popularity, the website ' s response time has slowed. The database is overloaded. The company cannot change the database and needs a solution that improves the response time of the Lambda function.
Which solution meets these requirements?
A developer has code that is stored in an Amazon S3 bucket. The code must be deployed as an AWS Lambda function across multiple accounts in the same AWS Region as the S3 bucket an AWS CloudPormation template that runs for each account will deploy the Lambda function.
What is the MOST secure way to allow CloudFormaton to access the Lambda Code in the S3 bucket?
A company wants to share information with a third party. The third party has an HTTP API endpoint that the company can use to share the information. The company has the required API key to access the HTTP API.
The company needs a way to manage the API key by using code. The integration of the API key with the application code cannot affect application performance.
Which solution will meet these requirements MOST securely?
A developer is using an AWS CloudFormation template to create a pipeline in AWS CodePipeline. The template creates an Amazon S3 bucket that the pipeline references in a source stage. The template also creates an AWS CodeBuild project for a build stage. The pipeline sends notifications to an Amazon SNS topic. Logs for the CodeBuild project are stored in Amazon CloudWatch Logs.
The company needs to ensure that the pipeline ' s artifacts are encrypted with an existing customer-managed AWS KMS key. The developer has granted the pipeline permissions to use the KMS key.
Which additional step will meet these requirements?
A company has an Amazon API Gateway REST API that integrates with an AWS Lambda function. The API’s development stage references a Lambda development alias named dev.
A developer needs to make a production alias of the Lambda function named prod available through the API.
Which solution meets these requirements?
A healthcare company is developing a multi-tier web application to manage patient records that are in an Amazon Aurora PostgreSQL database cluster. The company stores the application code in a Git repository and deploys the code to Amazon EC2 instances.
The application must comply with security policies and follow the principle of least privilege. The company must securely manage database credentials and API keys within the application code. The company must have the ability to rotate encryption keys on demand.
Which solution will meet these requirements?
A developer is designing an event-driven architecture. An AWS Lambda function that processes data needs to push processed data to a subset of four consumer Lambda functions. The data must be routed based on the value of one field in the data.
Which solution will meet these requirements with the LEAST operational overhead?
A developer is creating an application that will be deployed on IoT devices. The application will send data to a RESTful API that is deployed as an AWS Lambda function. The application will assign each API request a unique identifier. The volume of API requests from the application can randomly increase at any given time of day.
During periods of request throttling, the application might need to retry requests. The API must be able to handle duplicate requests without inconsistencies or data loss.
Which solution will meet these requirements?
A developer is storing sensitive data generated by an application in Amazon S3. The developer wants to encrypt the data at rest. A company policy requires an audit trail of when the AWS Key Management Service (AWS KMS) key was used and by whom.
Which encryption option will meet these requirements?
A company has a two-tier application that runs on Amazon EC2 instances behind an Application Load Balancer (ALB). The EC2 instances are in an Auto Scaling group. The Auto Scaling group is configured with a lifecycle hook that uses the default health checks for the EC2 instances.
During a recent change deployment, the ALB reported HTTP 502 errors. When a developer checked the target group, some of the EC2 instances were marked as unhealthy. However, the Auto Scaling group was not replacing the unhealthy EC2 instances.
Which configuration change should the developer make to replace the unhealthy EC2 instances?
An ecommerce company uses a set of AWS Lambda functions to process orders. The Lambda functions send logs to an Amazon CloudWatch Logs log group. The company observes timeout issues for one recently deployed processing function. The company needs to debug and identify the root cause of the timeout issue. The Lambda function is already in production. The company wants to have a live feed of filtered logs that start with the word " ERROR " to identify the root cause of the issue. The company wants to review only relevant log lines in near real time. Which solution will meet these requirements?
An application development team decides to use AWS X-Ray to monitor application code to analyze performance and perform root cause analysis.
What does the team need to do to begin using X-Ray? (Select TWO.)
A developer is building an application that processes a stream of user-supplied data. The data stream must be consumed by multiple Amazon EC2-based processing applications in parallel and in real time. Each processor must be able to resume without losing data if there is a service interruption. The application architect plans to add other processors in the near future and wants to minimize the amount of data duplication involved.
Which solution will satisfy these requirements?
A healthcare company uses AWS Amplify to host a patient management system. The system uses Amazon API Gateway to expose RESTful APIs. The backend logic of the system is handled by AWS Lambda functions.
One of the Lambda functions receives patient data that includes personally identifiable information (PII). The Lambda function sends the patient data to an Amazon DynamoDB table. The company must encrypt all patient data at rest and in transit before the data is stored in DynamoDB.
Which solution will meet these requirements?
A developer is building an application that stores user activity data in an Amazon DynamoDB table. The developer is writing a new AWS Lambda function to process the activity data. The developer grants the IAM role that the function assumes permission to query the table. The developer must ensure that the function does not have access to personally identifiable information (PII) that is stored in some of the table item attributes.
Which solutions will meet these requirements? (Select TWO.)
A developer needs to retrieve all data from an Amazon DynamoDB table that matches a particular partition key.
Which solutions will meet this requirement in the MOST operationally efficient way? (Select TWO.)
A developer has created a repository in AWS CodeArtifact . The development team needs to receive notifications when new packages are published to the repository.
Which solution will meet this requirement with the LEAST operational overhead ?
A developer is working on a web application that requires selective activation of specific features. The developer wants to keep the features hidden from end users until the features are ready for public access. Which solution will meet these requirements?
A developer is working on an application that handles 10 MB documents that contain highly sensitive data. The application will use AWS KMS to perform client-side encryption.
What steps must be followed?
A company has many microservices that are comprised of AWS Lambda functions. Multiple teams within the company split ownership of the microservices.
An application reads configuration values from environment variables that are contained in the Lambda functions. During a security audit, the company discovers that some of the environment variables contain sensitive information.
The company ' s security policy requires each team to have full control over the rotation of AWS KMS keys that the team uses for its respective microservices.
Which solution will meet these requirements?
A developer owns and supports an application that has database credentials stored in environment variables for AWS Lambda functions. The developer needs an alternate storage method for the credentials instead of using plaintext environment variables. Which solution will handle the credentials MOST securely?
A developer is creating an AWS Lambda function in VPC mode An Amazon S3 event will invoke the Lambda function when an object is uploaded into an S3 bucket The Lambda function will process the object and produce some analytic results that will be recorded into a file Each processed object will also generate a log entry that will be recorded into a file.
Other Lambda functions. AWS services, and on-premises resources must have access to the result files and log file. Each log entry must also be appended to the same shared log file. The developer needs a solution that can share files and append results into an existing file.
Which solution should the developer use to meet these requirements?
A company runs a new application on AWS Elastic Beanstalk. The company needs to deploy updates to the application. The updates must not cause any downtime for application users. The deployment must forward a specified percentage of incoming client traffic to a new application version during an evaluation period.
Which deployment type will meet these requirements?
A company runs an application on AWS The application uses an AWS Lambda function that is configured with an Amazon Simple Queue Service (Amazon SQS) queue called high priority queue as the event source A developer is updating the Lambda function with another SQS queue called low priority queue as the event source The Lambda function must always read up to 10 simultaneous messages from the high priority queue before processing messages from low priority queue. The Lambda function must be limited to 100 simultaneous invocations.
Which solution will meet these requirements ' ?
A company needs to distribute firmware updates to its customers around the world.
Which service will allow easy and secure control of the access to the downloads at the lowest cost?
A developer is working on an AWS Lambda function that accesses Amazon DynamoDB. The Lambda function must retrieve an item and update some of its attributes, or create the item if it does not exist. The Lambda function has access to the primary key.
Which IAM permissions should the developer request for the Lambda function to achieve this functionality?
A)
B)
C)
D)
A company is developing a serverless application that requires storage of sensitive API keys as environment variables for various services. The application requires the automatic rotation of the encryption keys every year.
Which solution will meet these requirements with no development effort?
A developer needs to build an AWS CloudFormation template that self-populates the AWS Region variable that deploys the CloudFormation template
What is the MOST operationally efficient way to determine the Region in which the template is being deployed?
A developer uses AWS IAM Identity Center to interact with the AWS CLI and AWS SDKs on a local workstation. API calls to AWS services were working when the SSO access was first configured. However, the developer is now receiving Access Denied errors. The developer has not changed any configuration files or scripts that were previously working on the workstation.
What is the MOST likely cause of the developer ' s access issue?
An application uses Amazon API Gateway integrated with an AWS Lambda function. Some API requests return HTTP 504 (Gateway Timeout) errors.
The Lambda function timeout is set to 20 seconds . The API Gateway integration timeout is 15 seconds . There are no errors in the Lambda logs.
Which solution will prevent the HTTP 504 errors?
A company runs continuous integration/continuous delivery (CI/CD) pipelines for its application on AWS CodePipeline. A developer must write unit tests and run them as part of the pipelines before staging the artifacts for testing.
How should the developer incorporate unit tests as part of CI/CD pipelines?
A developer is building various microservices for an application that will run on Amazon EC2 instances. The developer needs to monitor the end-to-end view of the requests between the microservices and debug any issues in the various microservices.
What should the developer do to accomplish these tasks?
For a deployment using AWS Code Deploy, what is the run order of the hooks for in-place deployments?
A company is running a custom web application on Amazon EC2 instances behind an Application Load Balancer. The instances run in an Auto Scaling group. The company ' s development team is using AWS CloudFormation to deploy all the services. The application is time-consuming to install and configure when the development team launches a new instance.
Which combination of steps should a developer take to optimize the performance when a new instance is launched? (Select TWO.)
A developer is building a multi-tenant application that uses an AWS Lambda function and an Amazon S3 bucket. An S3 event notification invokes the Lambda function when a new file is uploaded to the S3 bucket. The function reads each new file from the S3 bucket, processes the file, and writes data to an Amazon DynamoDB table. Each file in the S3 bucket has a prefix that corresponds with the name of the tenant that owns the file. Items in the DynamoDB table use tenant name as the partition key.
The developer must reduce the risk that file data will leak across tenants during processing.
Which combination of actions will meet this requirement? (Select THREE.)
A developer has deployed an AWS Lambda function that is subscribed to an Amazon Simple Notification Service {Amazon SNS) topic. The developer must implement a solution to add a record of each Lambda function invocation to an Amazon Simple Queue Service {Amazon SQS) queue.
Which solution will meet this requirement?
An application uses AWS X-Ray to generate a large amount of trace data on an hourly basis. A developer wants to use filter expressions to limit the returned results through user-specified custom attributes.
How should the developer use filter expressions to filter the results in X-Ray?
A company has an application that uses an AWS Lambda function to process customer orders. The company notices that the application processes some orders more than once.
A developer needs to update the application to prevent duplicate processing.
Which solution will meet this requirement with the LEAST implementation effort?
In a move toward using microservices, a company ' s management team has asked all development teams to build their services so that API requests depend only on that service ' s data store. One team is building a Payments service which has its own database; the service needs data that originates in the Accounts database. Both are using Amazon DynamoDB.
What approach will result in the simplest, decoupled, and reliable method to get near-real time updates from the Accounts database?
A company is concerned that a malicious user could deploy unauthorized changes to the code for an AWS Lambda function. What can a developer do to ensure that only trusted code is deployed to Lambda?
A developer is building an application on a fleet of Amazon EC2 Linux instances that run the Apache web server. The application must send API calls that contain sensitive customer data to a second fleet of Linux instances that also run Apache. The two fleets are deployed in peered VPCs within the same AWS account and AWS Region.
All sensitive data must be encrypted in transit .
Which solution will meet these requirements in the MOST operationally efficient way?
A developer is building a web and mobile application and needs a solution to deploy the application code. The solution must be compatible with the developer ' s Git source control repository. When the developer adds a new branch, the solution must create a separate deployment.
Which solution will meet these requirements with the LEAST operational overhead?
A company has a web application that is hosted on Amazon EC2 instances The EC2 instances are configured to stream logs to Amazon CloudWatch Logs The company needs to receive an Amazon Simple Notification Service (Amazon SNS) notification when the number of application error messages exceeds a defined threshold within a 5-minute period
Which solution will meet these requirements?
An application is using Amazon Cognito user pools and identity pools for secure access. A developer wants to integrate the user-specific file upload and download features in the application with Amazon S3. The developer must ensure that the files are saved and retrieved in a secure manner and that users can access only their own files. The file sizes range from 3 KB to 300 MB.
Which option will meet these requirements with the HIGHEST level of security?
A developer is working on a web application that runs on Amazon ECS and uses an Amazon DynamoDB table to store data. The application performs a large number of read requests against a small set of the table data.
How can the developer improve the performance of these requests? (Select TWO.)
A company is building a serverless application that uses AWS Lambda functions. The company needs to create a set of test events to test Lambda functions in a development environment. The test events will be created once and then will be used by all the developers in an 1AM developer group. The test events must be editable by any of the 1AM users in the 1AM developer group.
Which solution will meet these requirements?
A company hosts its application in the us-west-1 Region. The company wants to add redundancy in the us-east-1 Region. The application secrets are stored in AWS Secrets Manager in us-west-1. A developer needs to replicate the secrets to us-east-1.
Which solution will meet this requirement?
A company is creating an AWS Step Functions state machine to run a set of tests for an application. The tests need to run when a specific AWS Cloud Formation stack is deployed.
Which combination of steps will meet these requirements? (Select TWO.)
A developer is using an AWS account to build an application that stores files in an Amazon S3 bucket. Files must be encrypted at rest by AWS KMS keys. A second AWS account must have access to read files from the bucket.
The developer wants to minimize operational overhead for the application.
Which combination of solutions will meet these requirements? (Select TWO.)
A developer has created a large AWS Lambda function. Deployment of the function Is failing because of an InvalidParameterValueException error. The error message indicates that the unzipped size of the function exceeds the maximum supported value.
Which actions can the developer take to resolve this error? (Select TWO.)
A developer is building a new application on AWS. The application uses an AWS Lambda function that retrieves information from an Amazon DynamoDB table. The developer hardcoded the DynamoDB table name into the Lambda function code. The table name might change over time. The developer does not want to modify the Lambda code if the table name changes.
Which solution will meet these requirements MOST efficiently?
A developer writes an AWS Lambda function that processes new object uploads to an Amazon S3 bucket. The Lambda function runs for approximately 30 seconds. The function runs as expected under normal load conditions. Other Lambda functions in the AWS account also run as expected.
Occasionally, up to 500 new objects are written to the bucket every minute. Each new object write invokes the processing Lambda function during the high-volume periods through an event notification.
The developer must ensure that the processing function continues to run as expected during the high-volume periods.
Which solution will meet this requirement?
A company has implemented AWS CodeDeploy as part of its CI/CD pipeline. The company uses automatic rollbacks during an in-place deployment of a new version of a web application on Amazon EC2 instances.
What happens if the deployment of the new version fails validation ?
A company is expanding the compatibility of its photo-snaring mobile app to hundreds of additional devices with unique screen dimensions and resolutions. Photos are stored in Amazon S3 in their original format and resolution. The company uses an Amazon CloudFront distribution to serve the photos The app includes the dimension and resolution of the display as GET parameters with every request.
A developer needs to implement a solution that optimizes the photos that are served to each device to reduce load time and increase photo quality.
Which solution will meet these requirements MOST cost-effective?
A developer is creating a serverless application that uses an AWS Lambda function The developer will use AWS CloudFormation to deploy the application The application will write logs to Amazon CloudWatch Logs The developer has created a log group in a CloudFormation template for the application to use The developer needs to modify the CloudFormation template to make the name of the log group available to the application at runtime
Which solution will meet this requirement?
A developer is creating an Amazon DynamoDB table by using the AWS CLI The DynamoDB table must use server-side encryption with an AWS owned encryption key
How should the developer create the DynamoDB table to meet these requirements?
A company has deployed an application on AWS Elastic Beanstalk. The company has configured the Auto Scaling group that is associated with the Elastic Beanstalk environment to have five Amazon EC2 instances. If the capacity is fewer than four EC2 instances during the deployment, application performance degrades. The company is using the all-at-once deployment policy.
What is the MOST cost-effective way to solve the deployment issue?
A developer is troubleshooting a three-tier application, which is deployed on Amazon EC2 instances. There is a connectivity problem between the application servers and the database servers.
Which AWS services or tools should be used to identify the faulty component? (Select TWO.)
A company maintains a REST service using Amazon API Gateway and the API Gateway native API key validation. The company recently launched a new registration page, which allows users to sign up for the service. The registration page creates a new API key using CreateApiKey and sends the new key to the user. When the user attempts to call the API using this key. the user receives a 403 Forbidden error. Existing users are unaffected and can still call the API.
What code updates will grant these new users access to the API?
A developer maintains an Amazon API Gateway REST API. Customers use the API through a frontend UI and Amazon Cognito authentication.
The developer has a new version of the API that contains new endpoints and backward-incompatible interface changes. The developer needs to provide beta access to other developers on the team without affecting customers.
Which solution will meet these requirements with the LEAST operational overhead?
A developer must securely access a secret during a build process in an AWS CodeBuild project that has an IAM role. The secret must remain encrypted at rest and must be passed to the buildspec.yml file without appearing in build logs .
Which solution will meet these requirements with the LEAST operational overhead ?
A financial services company builds a credit card transaction processing application that uses an Amazon API Gateway HTTP API and AWS Lambda functions. The application logs all requests and request parameters to Amazon CloudWatch. The application makes the logs accessible to developer AWS accounts and a separate fraud detection AWS account by using a cross-account IAM role .
The company requires that only the fraud detection account be able to view customer credit card numbers that are associated with the transactions. Developers at the company must not be able to use the credit card numbers for testing or debugging.
The developers create the following data protection policy document snippet:
{
" Name " : " data-protection-policy " ,
" Description " : " Credit card redaction " ,
" Version " : " 2021-06-01 " ,
" Statement " : [{
" Sid " : " redact-policy " ,
" DataIdentifier " : [
" arn:aws:dataprotection::aws:data-identifier/CreditCardNumber "
],
" Operation " : {
" Deidentify " : {
" MaskConfig " : {}
}
}
}]
}
Which combination of actions must the developers take to comply with the new policy? (Select TWO.)
A company has implemented AWS CodeDeploy as part of its continuous integration and continuous delivery (CI/CD) stack in the cloud. The company sets up automatic rollbacks while initiating an in-place deployment of a new version of its web application on Amazon EC2 instances. Which result occurs if the deployment of the new version fails validation?
A software company is launching a multimedia application. The application will allow guest users to access sample content before the users decide if they want to create an account to gain full access. The company wants to implement an authentication process that can identify users who have already created an account. The company also needs to keep track of the number of guest users who eventually create an account.
Which combination of steps will meet these requirements? {Select TWO.)
A company uses Amazon API Gateway to expose a set of APIs to customers. The APIs have caching enabled in API Gateway. Customers need a way to invalidate the cache for each API when they test the API.
What should a developer do to give customers the ability to invalidate the API cache?
A developer manages an application that stores user objects in an Amazon S3 bucket without versioning enabled. The application has premium users and basic users.
After premium users upload objects, the premium users have unlimited downloads of their objects. Their objects are stored with a premium/ prefix. After basic users upload objects, the basic users can download their objects for 90 days. Their objects are stored with a basic/ prefix.
The developer needs to implement a solution to automatically delete objects for the basic users after 90 days.
Which solution will meet these requirements with the LEAST development effort?
A developer is creating an AWS Lambda function that searches for items from an Amazon DynamoDB table that contains customer contact information- The DynamoDB table items have the customer ' s email_address as the partition key and additional properties such as customer_type, name, and job_tltle.
The Lambda function runs whenever a user types a new character into the customer_type text input The developer wants the search to return partial matches of all the email_address property of a particular customer_type The developer does not want to recreate the DynamoDB table.
What should the developer do to meet these requirements?
A developer created a Node.js-based AWS Lambda function by using a container image of an AWS OS-only base image. There is a new security patch for Node.js that must be patched to the new Lambda function.
Which solution will meet this requirement?
A company needs to package and deploy an application that uses AWS Lambda to compress and decompress video clips. The application uses a video codec library that is larger than 250 MB. The application uses the library to compress the videos before storage and to decompress the videos upon retrieval.
Users of a web-based music application are experiencing latency issues on one of the application ' s most popular pages. A developer identifies that the issue is caused by the slow load time of specific widgets that rank and sort various songs and albums.
The developer needs to ensure that the widgets load more quickly by using built-in, in-memory ranking and sorting techniques. The developer must ensure that the data remains up to date.
Which solution will meet these requirements with the LEAST latency ?
A company hosts its application on AWS. The application runs on an Amazon Elastic Container Service (Amazon ECS) cluster that uses AWS Fargate. The cluster runs behind an Application Load Balancer The application stores data in an Amazon Aurora database A developer encrypts and manages database credentials inside the application
The company wants to use a more secure credential storage method and implement periodic credential rotation.
Which solution will meet these requirements with the LEAST operational overhead?
A developer needs to use Amazon DynamoDB to store customer orders. The developer ' s company requires all customer data to be encrypted at rest with a key that the company generates.
What should the developer do to meet these requirements?
A developer created an AWS Lambda function to process data in an application. The function pulls large objects from an Amazon S3 bucket, processes the data, and loads the processed data into a second S3 bucket. Application users have reported slow response times. The developer checks the logs and finds that Lambda function invocations run much slower than expected. The function itself is simple and has a small deployment package. The function initializes quickly. The developer needs to improve the performance of the application. Which solution will meet this requirement with the LEAST operational overhead?
A company is using AWS CloudFormation to deploy a two-tier application. The application will use Amazon RDS as its backend database. The company wants a solution that will randomly generate the database password during deployment. The solution also must automatically rotate the database password without requiring changes to the application.
What is the MOST operationally efficient solution that meets these requirements ' ?
A bookstore has an ecommerce website that stores order information in an Amazon DynamoDB table named BookOrders. The DynamoDB table contains approximately one million records.
The table uses OrderID as a partition key. There are no other indexes.
A developer wants to build a new reporting feature to retrieve all records from the table for a specified customer, based on a CustomerID property.
A developer is working on a web application that requires selective activation of features . Features must remain hidden from end users until they are ready for release.
Which solution will meet these requirements?
A team has an Amazon API Gateway REST API that consists of a single resource and a GET method that is backed by an AWS Lambda integration.
A developer makes a change to the Lambda function and deploys the function as a new version. The developer needs to set up a process to test the new version of the function before using the new version in production. The tests must not affect the production REST API.
Which solution will meet these requirements with the LEAST operational overhead?
A company has an application that is hosted on Amazon EC2 instances The application stores objects in an Amazon S3 bucket and allows users to download objects from the S3 bucket A developer turns on S3 Block Public Access for the S3 bucket After this change, users report errors when they attempt to download objects The developer needs to implement a solution so that only users who are signed in to the application can access objects in the S3 bucket.
Which combination of steps will meet these requirements in the MOST secure way? (Select TWO.)
A developer is writing an application that will provide data files to an external company. The external company needs to verify that the data is not modified in transit.
How can the developer use AWS KMS to prove the integrity of the transferred data?
A developer is building a solution to give an application that runs on an ecommerce platform the ability to send notifications. The application needs to call an API to send thousands of notifications each second to an HTTP endpoint. The notifications must be delivered in order. The developer must be able to filter out some of the notifications before sending them to the endpoint. Which solution will meet these requirements?
A company has an application that consists of different microservices that run inside an AWS account. The microservices are running in containers inside a single VPC. The number of microservices is constantly increasing. A developer must create a central logging solution for application logs.
Which solution will meet these requirements?
A company runs a payment application on Amazon EC2 instances behind an Application Load Balance The EC2 instances run in an Auto Scaling group across multiple Availability Zones The application needs to retrieve application secrets during the application startup and export the secrets as environment variables These secrets must be encrypted at rest and need to be rotated every month.
Which solution will meet these requirements with the LEAST development effort?
A company runs a serverless application on AWS. The application includes an AWS Lambda function. The Lambda function processes data and stores the data in an Amazon RDS for PostgreSQL database. A developer created user credentials in the database for the application.
The developer needs to use AWS Secrets Manager to manage the user credentials. The password must be rotated on a regular basis. The solution needs to ensure that there is high availability and no downtime for the application during secret rotation.
What should the developer do to meet these requirements?
A company has deployed infrastructure on AWS. A development team wants to create an AWS Lambda function that will retrieve data from an Amazon Aurora database. The Amazon Aurora database is in a private subnet in company ' s VPC. The VPC is named VPC1. The data is relational in nature. The Lambda function needs to access the data securely.
Which solution will meet these requirements?
A developer at a company needs to create a small application that makes the same API call once each day at a designated time. The company does not have infrastructure in the AWS Cloud yet, but the company wants to implement this functionality on AWS.
Which solution meets these requirements in the MOST operationally efficient manner?
A developer has designed an application to store incoming data as JSON files in Amazon S3 objects. Custom business logic in an AWS Lambda function then transforms the objects, and the Lambda function loads the data into an Amazon DynamoDB table. Recently, the workload has experienced sudden and significant changes in traffic. The flow of data to the DynamoDB table is becoming throttled.
The developer needs to implement a solution to eliminate the throttling and load the data into the DynamoDB table more consistently.
Which solution will meet these requirements?
A company has a two-tier application that consists of a frontend application and an Amazon RDS for MySQL database. The frontend application retrieves data from the database. The data consists of postal codes and their associated geographic coordinates. The application performs many more database reads than writes. The application retrieves each postal code from the database thousands of times each day.
A developer must improve the performance of the application to decrease latency.
Which change should the developer make to the application to meet these requirements?
An online food company provides an Amazon API Gateway HTTP API 1o receive orders for partners. The API is integrated with an AWS Lambda function. The Lambda function stores the orders in an Amazon DynamoDB table.
The company expects to onboard additional partners Some to me panthers require additional Lambda function to receive orders. The company has created an Amazon S3 bucket. The company needs 10 store all orders and updates m the S3 bucket for future analysis
How can the developer ensure that an orders and updates are stored to Amazon S3 with the LEAST development effort?
A developer is running an application on an Amazon EC2 instance. When the application attempts to read from an Amazon S3 bucket, the request fails. The developer determines that the IAM role associated with the EC2 instance is missing the required Amazon S3 read permissions.
The developer must grant the application access to read from the S3 bucket with the LEAST application disruption .
Which solution will meet this requirement?
A company deploys a new application to AWS. The company is streaming application logs to Amazon CloudWatch Logs. The company ' s development team must receive notification by email when the word " ERROR " appears in any log lines. A developer sets up an Amazon SNS topic and subscribes the development team to the topic.
What should the developer do next to meet the requirements?
A company stores all personally identifiable information (PII) in an Amazon DynamoDB table named PII in Account A. Developers are working on an application that is running on Amazon EC2 instances in Account B. The application in Account B requires access to the PII table.
An administrator in Account A creates an IAM role named AccessPII that has permission to access the PII table. The administrator also creates a trust policy that specifies Account B as a principal that can assume the role.
Which combination of steps should the developers take in Account B to allow their application to access the PII table? (Select TWO.)
A developer is creating an ecommerce workflow in an AWS Step Functions state machine that includes a HTTP Task state. The task passes shipping information and order details to an endpoint.
The developer needs to test the workflow to confirm that the HTTP headers and body are correct and that the responses meet expectations.
An application routinely processes a large number of Amazon S3 GET requests each second. A developer wants to increase the number of requests that the application can handle in parallel.
What should the developer do to achieve this goal?
A mobile app stores blog posts in an Amazon DynacnoDB table Millions of posts are added every day and each post represents a single item in the table. The mobile app requires only recent posts. Any post that is older than 48 hours can be removed.
What is the MOST cost-effective way to delete posts that are older man 48 hours?
A developer needs to automate deployments for a serverless, event-based workload. The developer needs to create standardized templates to define the infrastructure and to test the functionality of the workload locally before deployment.
The developer already uses a pipeline in AWS CodePipeline. The developer needs to incorporate any other infrastructure changes into the existing pipeline.
Which solution will meet these requirements?
A company is migrating its PostgreSQL database into the AWS Cloud. The company wants to use a database that will secure and regularly rotate database credentials. The company wants a solution that does not require additional programming overhead.
Which solution will meet these requirements?
A developer is creating a simple proof-of-concept demo by using AWS CloudFormation and AWS Lambda functions The demo will use a CloudFormation template to deploy an existing Lambda function The Lambda function uses deployment packages and dependencies stored in Amazon S3 The developer defined anAWS Lambda Function resource in a CloudFormation template. The developer needs to add the S3 bucket to the CloudFormation template.
What should the developer do to meet these requirements with the LEAST development effort?
A company is planning to deploy an application on AWS behind an Elastic Load Balancing (ELB) load balancer. The application uses an HTTP/HTTPS listener and must access the client IP addresses.
Which load-balancing solution meets these requirements?
A developer is creating a microservices application that runs across multiple compute environments. The application must securely access secrets that are stored in AWS Secrets Manager with minimal network latency. The developer wants a solution that reduces the number of direct calls to Secrets Manager and simplifies secrets management across environments. Which solution will meet these requirements with the LEAST operational overhead?
A developer is troubleshooting an application mat uses Amazon DynamoDB in the uswest-2 Region. The application is deployed to an Amazon EC2 instance. The application requires read-only permissions to a table that is named Cars The EC2 instance has an attached IAM role that contains the following IAM policy.
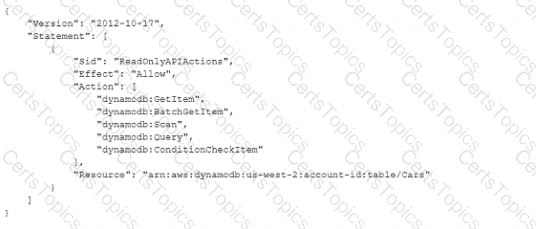
When the application tries to read from the Cars table, an Access Denied error occurs.
How can the developer resolve this error?
A company is creating an application that processes csv files from Amazon S3 A developer has created an S3 bucket The developer has also created an AWS Lambda function to process the csv files from the S3 bucket
Which combination of steps will invoke the Lambda function when a csv file is uploaded to Amazon S3? (Select TWO.)
A developer deploys an AWS Lambda function that writes data to Amazon DynamoDB. Amazon CloudWatch metrics show that some Lambda invocations result in errors. However, no CloudWatch log entries exist for the function. The function source code includes logging statements before the write operation.
What should the developer do to resolve the missing CloudWatch Logs entries?
A developer is deploying an application on Amazon EC2 instances that run in Account A. In certain cases, this application needs to read data from a private Amazon S3 bucket in Account B. The developer must provide the application access to the S3 bucket without exposing the S3 bucket to anyone else.
Which combination of actions should the developer take to meet these requirements? (Select TWO.)
An ecommerce company manages its application ' s infrastructure by using AWS Elastic Beanstalk. A developer wants to deploy the new version of the application with the least possible application downtime. The developer also must minimize the application ' s rollback time if there are issues with the deployment.
Which approach will meet these requirements?
A company offers a business-to-business software service that runs on dedicated infrastructure deployed in each customer ' s AWS account. Before a feature release, the company needs to run integration tests on real AWS test infrastructure. The test infrastructure consists of Amazon EC2 instances and an Amazon RDS database.
A developer must set up a continuous delivery process that will provision the test infrastructure across the different AWS accounts. The developer then must run the integration tests.
Which solution will meet these requirements with the LEAST administrative effort?
A company is building a content authoring application. The application has multiple user groups, such as content creator, reviewer, approver, and administrator. The company needs to assign users fine-grained permissions for specific parts of the application.
The company needs a solution to configure, maintain, and analyze user permissions. The company wants a solution that can be easily adapted to work with newer applications in the future. The company must use a third-party OpenID Connect (OIDC) identity provider (IdP) to authenticate users.
A company built an online event platform For each event the company organizes quizzes and generates leaderboards that are based on the quiz scores. The company stores the leaderboard data in Amazon DynamoDB and retains the data for 30 days after an event is complete The company then uses a scheduled job to delete the old leaderboard data
The DynamoDB table is configured with a fixed write capacity. During the months when many events occur, the DynamoDB write API requests are throttled when the scheduled delete job runs.
A developer must create a long-term solution that deletes the old leaderboard data and optimizes write throughput
Which solution meets these requirements?
A company runs a serverless application that uses several AWS Lambda functions. The existing Lambda functions run in a VPC. The Lambda functions query public APIs successfully.
To add a new feature to the application, a developer creates a new Lambda function to query external public APIs. The new Lambda function must store aggregated results in an Amazon RDS database that is in a private subnet of the VPC. The developer configures VPC access for the new Lambda function and sets up a working connection to the RDS database. The requests that the new Lambda function makes to the external APIs fail. However, requests from the developer’s local workstation to the same APIs are successful.
Which solution will meet this requirement?
A developer is storing JSON files in an Amazon S3 bucket. The developer wants to securely share an object with a specific group of people.
How can the developer securely provide temporary access to the objects that are stored in the S3 bucket?
A developer is testing an AWS Lambda function that has an event source of an Amazon SQS queue. The developer notices that some of the messages the Lambda function processes reappear in the queue while the messages are being processed. The developer must correct this behavior. Which solution will meet this requirement?
A developer is creating a service that uses an Amazon S3 bucket for image uploads. The service will use an AWS Lambda function to create a thumbnail of each image Each time an image is uploaded the service needs to send an email notification and create the thumbnail The developer needs to configure the image processing and email notifications setup.
Which solution will meet these requirements?
A developer is modifying an AWS Lambda function that accesses an Amazon RDS for MySQL database. The developer discovers that the Lambda function has the database credentials stored as plaintext in the Lambda function code.
The developer must implement a solution to make the credentials more secure. The solution must include automated credential rotation every 30 days.
Which solution will meet these requirements?
A company is using Amazon API Gateway to invoke a new AWS Lambda function The company has Lambda function versions in its PROD and DEV environments. In each environment, there is a Lambda function alias pointing to the corresponding Lambda function version API Gateway has one stage that is configured to point at the PROD alias
The company wants to configure API Gateway to enable the PROD and DEV Lambda function versions to be simultaneously and distinctly available
Which solution will meet these requirements?
A developer is using AWS Step Functions to automate a workflow The workflow defines each step as an AWS Lambda function task The developer notices that runs of the Step Functions state machine fail in the GetResource task with either an UlegalArgumentException error or a TooManyRequestsException error
The developer wants the state machine to stop running when the state machine encounters an UlegalArgumentException error. The state machine needs to retry the GetResource task one additional time after 10 seconds if the state machine encounters a TooManyRequestsException error. If the second attempt fails, the developer wants the state machine to stop running.
How can the developer implement the Lambda retry functionality without adding unnecessary complexity to the state machine ' ?
A developer is building an application that stores sensitive user data. The application includes an Amazon CloudFront distribution and multiple AWS Lambda functions that handle user requests.
User requests contain more than 20 data fields. Each application transaction includes sensitive data that must be encrypted. Only specific parts of the application must be able to decrypt the data.
Which solution will meet these requirements?
A developer writes an AWS Lambda function that processes new object uploads to an Amazon S3 bucket. The Lambda function runs for approximately 30 seconds. The function runs as expected under normal load conditions. Other Lambda functions in the AWS account also run as expected. Occasionally, up to 500 new objects are written to the bucket every minute. Each new object write invokes the processing Lambda function during the high-volume periods through an event. The developer must ensure that the processing function will continue to run as expected during the high-volume periods. Which solution will meet this requirement?
A developer is creating a new application that will be accessed by users through an API created using Amazon API Gateway. The users need to be authenticated by a third-party Security Assertion Markup Language (SAML) identity provider. Once authenticated, users will need access to other AWS services, such as Amazon S3 and Amazon DynamoDB.
How can these requirements be met?
A developer manages a serverless application that uses an AWS Lambda function. The application periodically interacts with an external API by using short-lived authentication keys . Currently, the developer embeds the authentication keys directly in the Lambda function code. This approach requires manual updates and introduces security risks and operational inefficiencies.
The developer needs a secure and automated solution for authentication key storage, retrieval, and rotation.
Which solution will meet these requirements?
A developer registered an AWS Lambda function as a target for an Application Load Balancer (ALB) using a CLI command. However, the Lambda function is not being invoked when the client sends requests through the ALB.
Why is the Lambda function not being invoked?
A developer received the following error message during an AWS CloudFormation deployment:
Which action should the developer take to resolve this error?
A company is building a scalable data management solution by using AWS services to improve the speed and agility of development. The solution will ingest large volumes of data from various sources and will process this data through multiple business rules and transformations.
The solution requires business rules to run in sequence and to handle reprocessing of data if errors occur when the business rules run. The company needs the solution to be scalable and to require the least possible maintenance.
Which AWS service should the company use to manage and automate the orchestration of the data flows to meet these requirements?
A developer designed an application on an Amazon EC2 instance The application makes API requests to objects in an Amazon S3 bucket
Which combination of steps will ensure that the application makes the API requests in the MOST secure manner? (Select TWO.)
A company is building an application to accept data from customers. The data must be encrypted at rest and in transit.
The application uses an Amazon API Gateway API that resolves to AWS Lambda functions. The Lambda functions store the data in an Amazon Aurora MySQL DB cluster. The application worked properly during testing.
A developer configured an Amazon CloudFront distribution with field-level encryption that uses an AWS Key Management Service (AWS KMS) key. After the configuration of the distribution, the application behaved unexpectedly. All the data in the database changed from plaintext to ciphertext.
The developer must ensure that the data is not stored in the database as the ciphertext from the CloudFront field-level encryption.
Which solution will meet this requirement?
A developer is using an AWS Lambda function to generate avatars for profile pictures that are uploaded to an Amazon S3 bucket. The Lambda function is automatically invoked for profile pictures that are saved under the /original/ S3 prefix. The developer notices that some pictures cause the Lambda function to time out. The developer wants to implement a fallback mechanism by using another Lambda function that resizes the profile picture.
Which solution will meet these requirements with the LEAST development effort?
A developer at a company needs to create a small application mat makes the same API call once each flay at a designated time. The company does not have infrastructure in the AWS Cloud yet, but the company wants to implement this functionality on AWS.
Which solution meets these requirements in the MOST operationally efficient manner?
A developer is designing a serverless application with two AWS Lambda functions to process photos. One Lambda function stores objects in an Amazon S3 bucket and stores the associated metadata in an Amazon DynamoDB table. The other Lambda function fetches the objects from the S3 bucket by using the metadata from the DynamoDB table. Both Lambda functions use the same Python library to perform complex computations and are approaching the quota for the maximum size of zipped deployment packages.
What should the developer do to reduce the size of the Lambda deployment packages with the LEAST operational overhead?
A developer is migrating a containerized application from an on-premises environment to the AWS Cloud. The developer is using the AWS CDK to provision a container in Amazon ECS on AWS Fargate. The container is behind an Application Load Balancer (ALB).
When the developer deploys the stack, the deployment fails because the ALB fails health checks. The developer needs to resolve the failed health checks.
Which solutions will meet this requirement? (Select TWO.)