Microsoft Related Exams
SC-200 Exam







The Microsoft SC-200 exam assesses your knowledge in various security operation domains, including:
CertsTopics offers high-quality SC-200 exam dumps, questions and answers, and practice tests tailored to the Microsoft Certified: Security Operations Analyst Associate Exam syllabus. Our SC-200 study materials come in PDF and testing engine formats, ensuring effective preparation and a high success rate.
You need to implement the Azure Information Protection requirements. What should you configure first?
You need to recommend a solution to meet the technical requirements for the Azure virtual machines. What should you include in the recommendation?
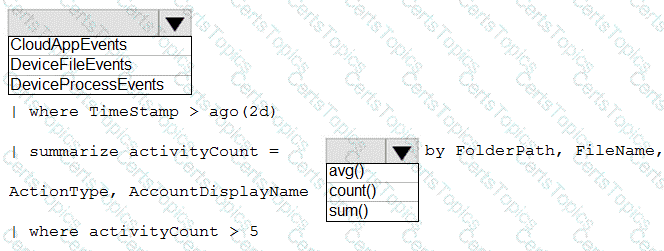
You need to create an advanced hunting query to i nvestigate the executive team issue.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.