Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Match the types of Conditional Access signals to the appropriate definitions.
To answer, drag the appropriate Conditional Access signal type from the column on the left to its definition on the right. Each signal type may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.

You are evaluating the compliance score in Microsoft Purview Compliance Manager.
Match the compliance score action subcategories to the appropriate actions.
To answer, drag the appropriate action subcategory from the column on the left to its action on the right. Each action subcategory may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.

What are two reasons to deploy multiple virtual networks instead of using just one virtual network? Each correct answer presents a complete solution.
NOTE; Each correct selection is worth one point.
Which statement represents a Microsoft privacy principle?
What is a function of Conditional Access session controls?
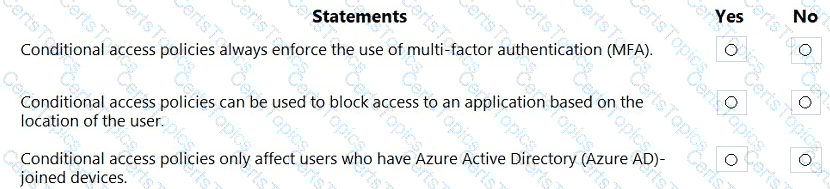
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
Select the answer that correctly completes the sentence.

What is an example of encryption at rest?
What is a use case for implementing information barrier policies in Microsoft 365?
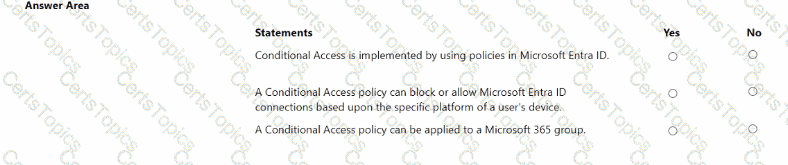
Match the Microsoft Defender for Office 365 feature to the correct description.
To answer, drag the appropriate feature from the column on the left to its description on the right. Each feature may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
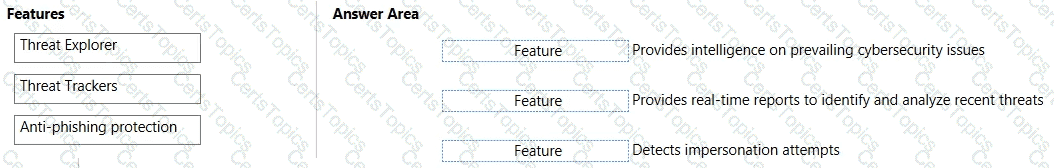
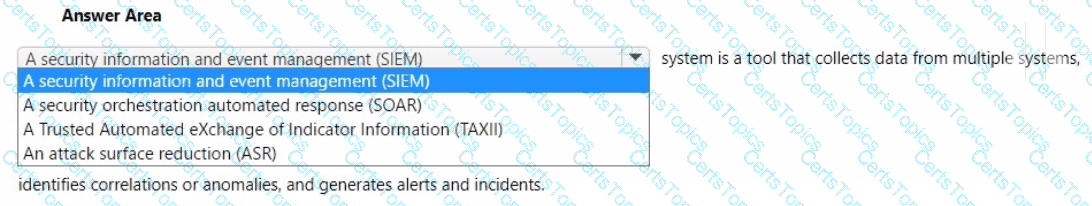
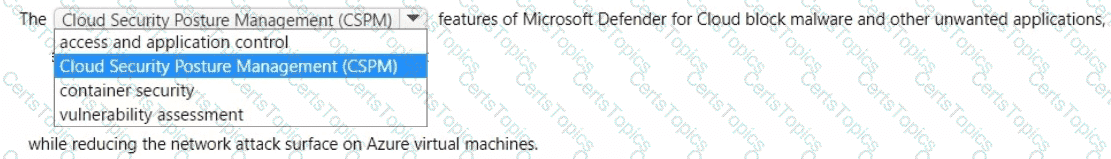
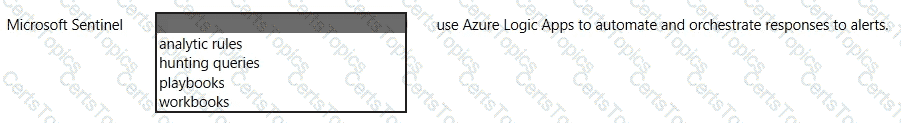
Select the answer that correctly completes the sentence.
Select the answer that correctly completes the sentence.
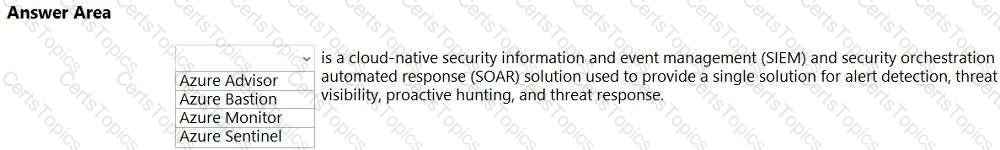
Select the answer that correctly completes the sentence.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

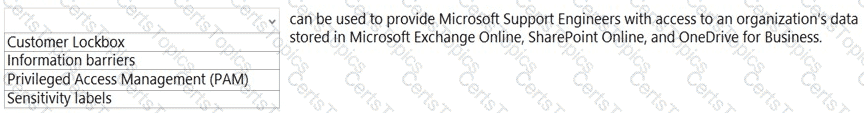
Select The answer that correctly completes the sentence.
Select the answer that correctly completes the sentence.

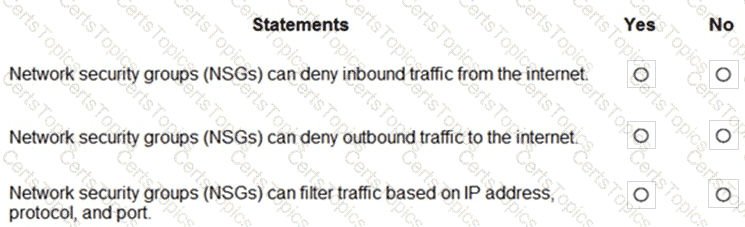
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

What can you protect by using the information protection solution in the Microsoft 365 compliance center?
Which three authentication methods does Windows Hello for Business support? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Which two types of devices can be managed by using Endpoint data loss prevention (Endpoint DLP)? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
Select the answer that correctly completes the sentence.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
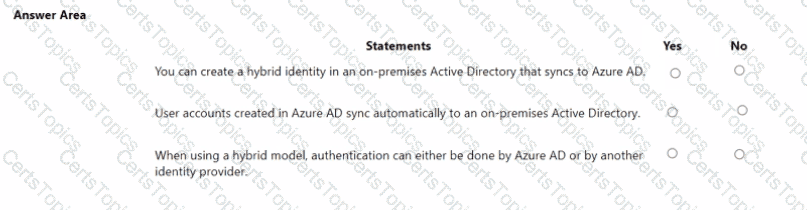
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

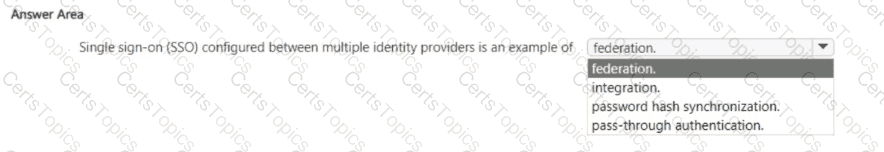
Select the answer that correctly completes the sentence.
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
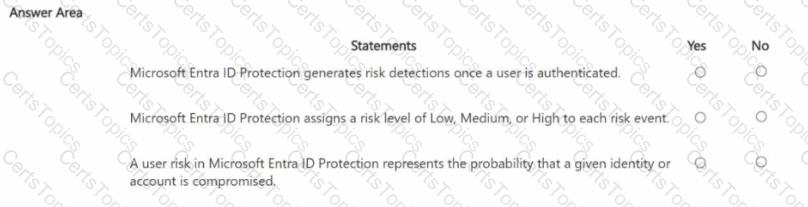
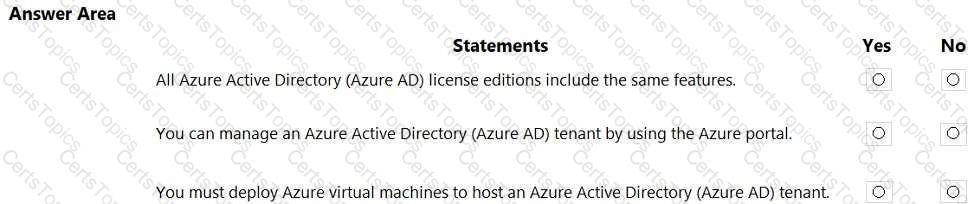
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

Which two actions can you perform by using Azure Key Vault? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
What can you use to provision Azure resources across multiple subscriptions in a consistent manner?
Which security feature is available in the free mode of Microsoft Defender for Cloud?
Select the answer that correctly completes the sentence.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point

Which Microsoft 365 compliance center feature can you use to identify all the documents on a Microsoft SharePoint Online site that contain a specific key word?
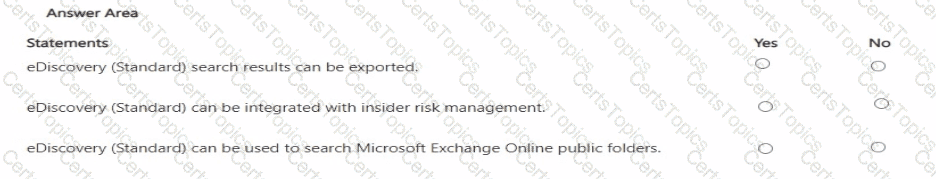
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
What feature in Microsoft Defender for Endpoint provides the first line of defense against cyberthreats by reducing the attack surface?
In a hybrid identity model, what can you use to sync identities between Active Directory Domain Services (AD DS) and Azure Active Directory (Azure AD)?
Which pillar of identity relates to tracking the resources accessed by a user?
Select the answer that correctly completes the sentence.

Which two tasks can you implement by using data loss prevention (DLP) policies in Microsoft 365? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
What is a characteristic of a sensitivity label in Microsoft 365?
Which feature is included in Microsoft Entra ID Governance?
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

Which Microsoft 365 feature can you use to restrict communication and the sharing of information between members of two departments at your organization?
Select the answer that correctly completes the sentence.

For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
What can you specify in Microsoft 365 sensitivity labels?
Select the answer that correctly completes the sentence.
Select the answer that correctly completes the sentence.

Which three authentication methods can be used by Azure Multi-Factor Authentication (MFA)? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
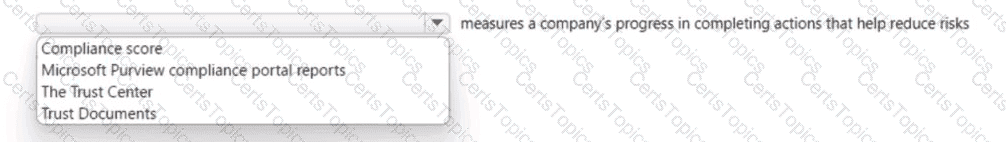
Which score measures an organization ' s progress in completing actions that help reduce risks associated to data protection and regulatory standards?
Select the answer that correctly completes the sentence.

Select the answer that correctly completes the sentence.

You need to connect to an Azure virtual machine by using Azure Bastion. What should you use?
You have a Microsoft 365 E3 subscription.
You plan to audit user activity by using the unified audit log and Basic Audit.
For how long will the audit records be retained?
Which two Azure resources can a network security group (NSG) be associated with? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
Which service includes Microsoft Secure Score for Devices?
You have an Azure subscription that contains multiple resources.
You need to assess compliance and enforce standards for the existing resources.
What should you use?
In the shared responsibility model, for what is Microsoft responsible when managing Azure virtual machines?
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

Which Microsoft Purview solution can be used to identify data leakage?
Which two types of resources can be protected by using Azure Firewall? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.